AI cloud security solutions for startups are no longer optional — they are the difference between survival and shutdown in 2026.
A startup lost six weeks of customer data in 2024 — not because of a sophisticated nation-state attack, but because a developer accidentally made an S3 bucket public during a late-night deployment. An automated scanner found it within four hours. The breach response cost $340,000. The company almost didn’t survive it.
This isn’t an edge case. It’s Tuesday.
If your startup runs on Amazon Web Services, Microsoft Azure, or Google Cloud, attackers are scanning your environment right now — automatically, continuously, and at scale. The question isn’t whether your cloud has vulnerabilities. It’s whether you’ll find them first.
Modern AI cloud security tools have fundamentally changed that equation. What once required a dedicated security operations center can now be automated, contextualized, and acted on in real time — even with a three-person DevOps team. This guide covers what these platforms do, which ones lead the market in 2026, how to implement them without slowing your team down, and what realistic limitations to plan around.
Why Startups Need AI-Powered Cloud Security Solutions
AI cloud security solutions for startups are essential because modern cloud environments generate more risk than small teams can manually manage. That assumption is exactly what attackers count on.
In most early-stage startups, security is treated as a Phase 2 problem — something to address after product-market fit, after the next funding round, after things settle down. The trouble is that cloud infrastructure never settles down. Engineers push microservices to production daily. Contractors get over-provisioned access and never get off-boarded. CI/CD pipelines accumulate plaintext API keys like technical debt. Each of these is an open door.
According to Verizon’s Data Breach Investigations Report, credential theft and cloud misconfiguration remain the top two breach vectors year after year — and startups are disproportionately represented precisely because they move fast and patch security gaps slowly. For a company on 18 months of runway, a significant breach doesn’t mean a bad quarter. It can mean shutting down.
Traditional security tools were designed for static, on-premise environments with predictable perimeters. They weren’t built for the elasticity, API-driven control planes, and ephemeral workloads of modern cloud infrastructure. That’s the core problem AI-driven cloud protection solves — bringing machine-speed threat detection to environments that move at machine speed.
Quick Answer — Why do startups need AI cloud security? Cloud environments generate more telemetry than human analysts can process, and threats move faster than manual response can contain. AI automates detection, triage, and response at cloud scale — making enterprise-grade security accessible to lean teams without a dedicated SOC.

What Are AI Cloud Security Platforms for Startups
AI cloud security solutions for startups use machine learning and automation to continuously detect and respond to threats across dynamic cloud environments.
At their core, these platforms ingest telemetry from cloud APIs, identity systems, network flows, workload logs, and storage activity. Trained ML models establish a dynamic baseline of normal behavior for your specific environment, then flag deviations that match known threat patterns or indicate novel attack techniques that signature-based tools would miss entirely.
A common mistake DevOps teams make is assuming their cloud provider’s native security tools — AWS Security Hub, Azure Defender, Google Security Command Center — are sufficient on their own. They aren’t. Native tools provide visibility within a single provider’s ecosystem. Dedicated AI security platforms provide correlated, cross-environment threat detection, behavioral baselining, and automated response that cloud-native tools simply aren’t designed to deliver.
Quick Answer — What are AI cloud security solutions? AI cloud security solutions are ML-powered platforms that continuously monitor cloud environments to detect, prioritize, and automatically respond to threats — replacing manual log review with intelligent, real-time defense that scales with your infrastructure.
Core capabilities of modern startup cloud security platforms:
- Cloud Security Posture Management (CSPM) — automated misconfiguration detection across all major providers
- Cloud Workload Protection (CWP) — runtime security for containers, VMs, and serverless functions
- Identity and Access Intelligence — continuous monitoring for credential abuse and privilege escalation
- AI anomaly detection — behavioral baselining with real-time deviation alerts
- Automated incident response — pre-built playbooks that trigger containment without human intervention
Major Cloud Security Risks Startups Face Without AI-Driven Cloud Protection
Cloud Misconfiguration Risks That AI Cloud Security Solutions for Startups Prevent
AI cloud security solutions for startups continuously scan for misconfigurations, preventing exposure before attackers can exploit them. An S3 bucket left publicly accessible, a security group with overly permissive inbound rules, a Kubernetes dashboard exposed to the internet — these errors are nearly inevitable when engineers are rewarded for shipping features, not auditing IAM policies.
Without AI-powered CSPM scanning continuously, a misconfigured resource can sit exposed for days. The Cloud Security Alliance consistently ranks misconfiguration as the top cloud threat across Amazon Web Services, Microsoft Azure, and Google Cloud environments alike. Without continuous AI scanning, you’re relying on periodic manual audits in an environment that changes every single day.
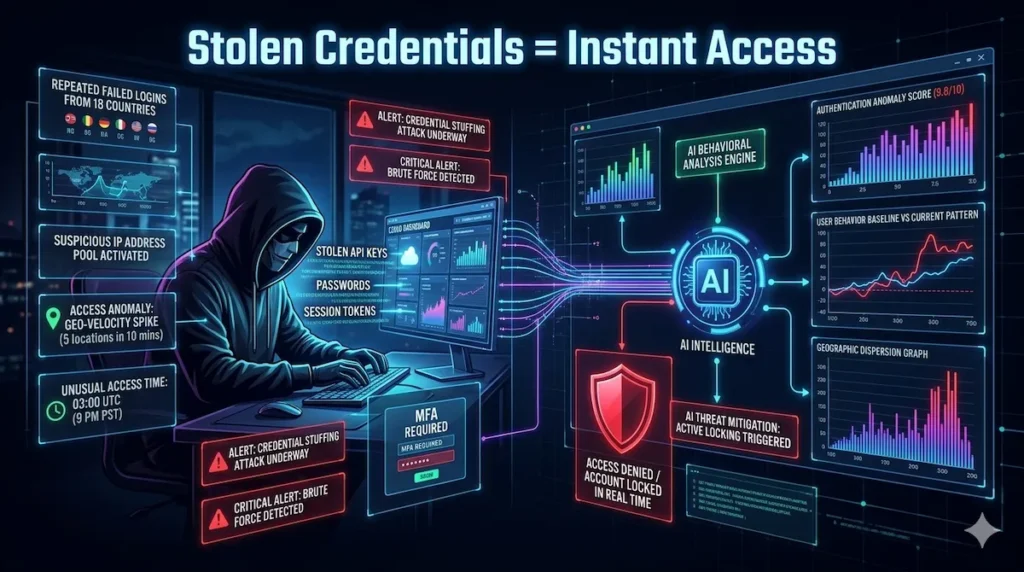
Credential Theft and Account Takeovers That Startup Cloud Security Tools Detect
In one audit of a Series A SaaS company, we found 14 active API keys committed to a public GitHub repository — keys that had been live for over eight months. Two had already been used by unauthorized parties to query production data. The company had no idea.
AI cloud security solutions for startups detect credential abuse by analyzing behavioral patterns across users and service accounts. Once an attacker holds a valid credential for your cloud console or CI/CD pipeline, lateral movement becomes straightforward. Without behavioral analytics tracking how each user and service account normally operates, you won’t detect an attacker logging in from a new IP at 3 AM and quietly downloading your database snapshots.
For a deeper look at how identity threats intersect with endpoint vectors, see our guide on AI endpoint security for startups.
API Exploits in Cloud Environments That AI-Powered Security Solutions Stop
AI cloud security solutions for startups monitor API activity in real time to detect anomalies and prevent unauthorized access. Cloud APIs managing infrastructure — like the Amazon Web Services EC2 API or Microsoft Azure Resource Manager — are high-value targets because they control compute, storage, and network resources directly. Attackers exploit broken object-level authorization, excessive data exposure, and injection vulnerabilities.
A compromised API key can provision crypto-mining infrastructure, exfiltrate customer data, or destroy production resources entirely before any alert fires. Without AI threat detection monitoring API call patterns for statistical anomalies, these attacks often go undetected until the damage is irreversible.
Ransomware Attacks on Cloud Storage That AI Cloud Security Solutions for Startups Block
AI cloud security solutions for startups identify ransomware behavior patterns early, enabling automated containment before data loss occurs. Sophisticated attackers disable versioning and delete backups before encrypting Amazon Web Services S3, Microsoft Azure Blob, or Google Cloud Storage — leaving companies with no recovery path and a ransom demand. AI-driven cloud monitoring detects the behavioral signatures of ransomware activity — bulk delete operations, rapid encryption events, unusual storage access patterns — and triggers automated containment before the damage becomes irreversible.
How AI Cloud Security Tools Detect Threats Faster
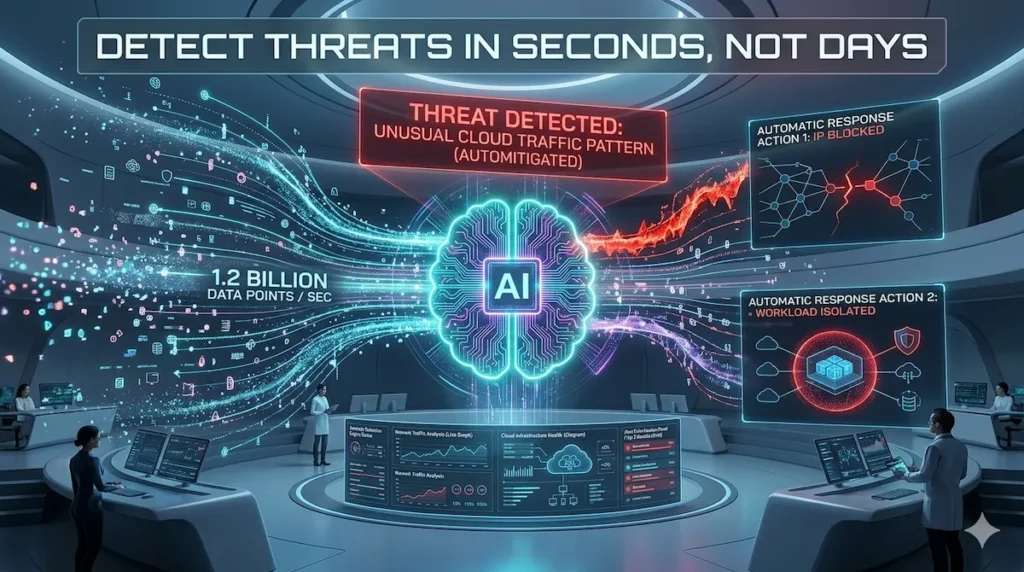
AI cloud security solutions for startups detect threats faster by combining behavioral analytics with real-time anomaly detection at cloud scale.
Behavioral Analytics in AI Cloud Security Platforms for Startups
AI cloud security solutions for startups rely on behavioral analytics to identify deviations from normal activity that signal potential attacks. Rather than relying solely on known threat signatures — which attackers actively evade — ML models learn what normal looks like for every user, service account, application, and infrastructure component in your specific environment.
This baseline is dynamic. It updates as your team grows, infrastructure scales, and usage patterns shift. When activity deviates from baseline in ways that correlate with known attack techniques — a service account calling APIs it has never previously used, a developer accessing production databases from a new geography at an unusual hour — the system generates a prioritized, contextualized alert rather than a raw log entry.
This is the core differentiation between modern AI cybersecurity platforms and legacy rule-based tools: instead of matching against a static list of known bad behaviors, they detect unknown threats through statistical deviation. Platforms like Lacework and CrowdStrike have invested heavily in this capability, making their behavioral engines among the most mature available.
Real-Time Anomaly Detection Using Startup AI Cloud Security Tools
AI cloud security solutions for startups use real-time anomaly detection to surface threats within minutes instead of hours or days.
For a startup running containerized workloads on Kubernetes across Amazon Web Services and Google Cloud, real-time cloud anomaly detection means knowing within minutes if a container begins communicating with a known command-and-control server — not during the next morning’s log review when the damage is already done.
To understand how detection capabilities compare technically across leading platforms, our AI-powered threat detection tools for startups breakdown covers the differences in depth.
Automated Incident Response in AI-Powered Cloud Security Solutions
AI cloud security solutions for startups automate incident response by triggering predefined actions the moment a threat is detected. AI platforms compress that timeline dramatically by triggering pre-defined response playbooks the moment specific threat conditions are met.
Common automated responses include revoking compromised credentials, quarantining affected workloads, blocking suspicious IPs at the network layer, and routing fully contextualized alerts to the on-call engineer. This level of cloud security automation converts a potential multi-day breach investigation into a contained incident resolved in hours — without a dedicated SOC team.
Best AI Cloud Security Solutions for Startups in 2026
Quick Answer — What are the best AI cloud security solutions for startups in 2026? The best AI cloud security solutions for startups in 2026 combine automation, multi-cloud visibility, and intelligent threat prioritization.
For a full side-by-side comparison with pricing tiers and feature matrices, see our startup cybersecurity software comparison for 2026.
Tool Comparison at a Glance
| Tool | Best For | Core Strength | Key Limitation | Pricing Tier |
|---|---|---|---|---|
| CrowdStrike Falcon | Series A+ startups | World-class threat intel + AI SOC monitoring | Premium cost; complex setup | $$$ |
| Prisma Cloud (Palo Alto Networks) | Compliance-focused, mid-stage | Broadest CNAPP coverage; DevSecOps integration | Steep learning curve; feature overload | $$$ |
| Wiz | Early-stage, speed-focused | Agentless deployment; contextual risk scoring | Runtime detection less mature | $$ |
| Lacework | Alert fatigue-weary teams | Behavioral analytics; false positive reduction | Narrower threat intel; ML ramp-up period | $$ |
CrowdStrike Falcon Cloud Security — Leading AI Cloud Security Platform for Startups
CrowdStrike Falcon extends industry-leading endpoint detection capabilities into cloud environments. Falcon Cloud Security provides runtime threat detection for containers and cloud workloads, CSPM across Amazon Web Services, Microsoft Azure, and Google Cloud, and deep integration with CrowdStrike‘s global threat intelligence network — one of the most comprehensive in the industry.
Strengths: World-class threat intelligence, excellent detection accuracy, strong automated incident response, and a well-regarded AI SOC monitoring experience. The OverWatch managed threat hunting service functions as an outsourced tier-3 SOC — particularly valuable for startups without in-house security analysts.
Limitations: Pricing sits at the premium end of the market. Initial configuration complexity can strain small DevOps teams. Budget 60–90 days for full deployment and tuning.
Best for: Growth-stage startups and Series A+ companies with a defined security budget and a need for best-in-class threat intelligence.
Prisma Cloud by Palo Alto Networks — Comprehensive AI-Driven Cloud Protection for Startups
Prisma Cloud by Palo Alto Networks covers CSPM, cloud workload protection, container security, API security, and data security posture management in a single integrated platform — a strong fit for startups preparing for enterprise sales cycles that include security questionnaires and compliance audits. Learn more at Palo Alto Networks’ official Prisma Cloud page.
Strengths: Exceptional coverage breadth, strong DevSecOps cloud security integration with CI/CD pipelines, and solid multi-cloud visibility. Infrastructure-as-code scanning catches misconfigurations before they reach production — a major win for teams using Terraform or CloudFormation.
Limitations: Significant configuration complexity. Smaller startups frequently pay for capabilities they don’t yet need. Full deployment requires dedicated time and expertise.
Best for: Mid-stage startups preparing for SOC 2 certification, ISO 27001 compliance, or enterprise customer security audits.
Wiz Cloud Security Platform — Agentless Startup Cloud Security Solution
Wiz was designed with developer and DevOps usability as a first principle. Its agentless architecture means deployment takes hours rather than weeks — a decisive advantage for teams that can’t afford lengthy implementation projects. Wiz provides full-stack cloud vulnerability scanning, CSPM, and contextual risk prioritization that shows actual exploitability — not just raw vulnerability counts. Visit Wiz’s official platform page for technical architecture details.
Strengths: Agentless deployment, excellent risk contextualization, strong developer-friendly workflows, and broad multi-cloud support across Amazon Web Services, Microsoft Azure, and Google Cloud.
Limitations: Runtime threat detection is less mature than CrowdStrike‘s. Best paired with a dedicated workload protection solution for comprehensive coverage.
Best for: Early-stage startups that need immediate cloud security visibility with minimal deployment friction.
Lacework AI Security Platform — Behavioral AI Cloud Security for Startups
Lacework built its platform around AI-driven behavioral analytics and cloud threat monitoring — specifically to address the alert fatigue that plagues teams using legacy SIEM tools. The Polygraph data platform provides compelling visualization of cloud activity relationships that helps teams understand threat context at a glance.
Strengths: Strong behavioral analytics, excellent false positive reduction, and comprehensive multi-cloud support across all three major providers.
Limitations: Threat intelligence breadth is narrower than CrowdStrike‘s. The initial ML training period requires patience before detection accuracy peaks.
Best for: Startups prioritizing behavioral anomaly detection and teams frustrated by high false positive rates from legacy security tools.
If budget is a key constraint, our guide to affordable cybersecurity tools for startups covers cost-effective alternatives and hybrid approaches at different funding stages.
How to Choose the Right Startup Cloud Security Platform
Choosing AI cloud security solutions for startups depends on automation level, pricing, and integration with your existing DevOps workflows.
Pricing and startup fit. Wiz and Lacework offer flexible, usage-based pricing with startup programs for early-stage companies. CrowdStrike and Prisma Cloud by Palo Alto Networks are premium products better suited to growth-stage startups with defined security budgets. Always negotiate — multi-year commitments typically unlock 20–40% discounts.
Automation capabilities. Evaluate how much threat detection and response the platform handles automatically versus requiring human review. For lean teams, higher automation directly reduces the operational burden on engineers already stretched thin.
Multi-cloud support. If you’re running workloads across Amazon Web Services, Microsoft Azure, and Google Cloud, verify consistent detection quality across all three providers. Coverage gaps in secondary cloud environments are a common and exploited blind spot.
DevOps integration. The best startup cloud security tools integrate naturally into existing developer workflows. Prioritize native integrations with your CI/CD pipeline, IaC tools like Terraform and CloudFormation, and incident management systems like PagerDuty and Jira. Security that creates developer friction gets disabled.
Scalability. Confirm the platform can handle the telemetry volume of a 10x larger environment without degraded performance or cost surprises at your next funding milestone.
For a structured comparison across all five dimensions, our best AI security tools for startups 2026 guide provides detailed platform scoring in each category.
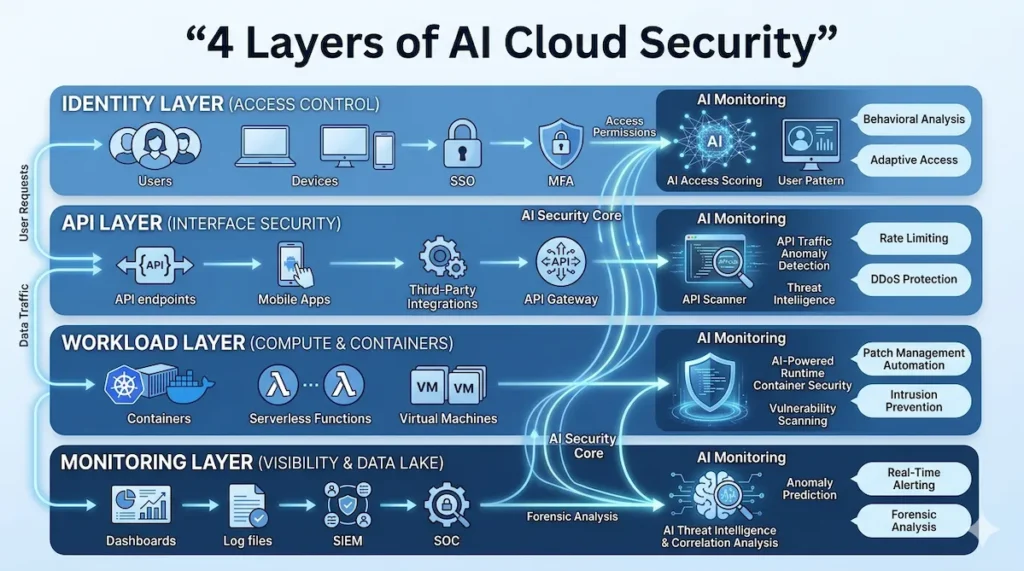
AI Cloud Security Architecture for Startups (Reference Model)
AI cloud security solutions for startups should be implemented across identity, workload, API, and monitoring layers for complete protection. A complete startup cloud security stack should address four core layers:
Identity Layer — Every user, service account, and API key accessing your cloud environment. AI monitoring here detects credential compromise, privilege escalation, and anomalous authentication. Key tools: Amazon Web Services IAM Access Analyzer, Microsoft Azure AD Identity Protection, Lacework.
Workload Layer — Containers, VMs, serverless functions, and Kubernetes clusters. AI workload protection monitors runtime behavior, detects malicious processes, and prevents lateral movement. Key tools: CrowdStrike Falcon, Prisma Cloud by Palo Alto Networks.
API Layer — Every surface where your applications communicate internally and externally. AI API security monitors call patterns, detects abuse, and enforces least-privilege policies programmatically. Key tools: Prisma Cloud API Security, Amazon Web Services API Gateway with WAF.
Monitoring Layer — The aggregation and analytics layer that ties identity, workload, and API signals together. This is where AI-driven correlation surfaces threats that span multiple layers. Key tools: Wiz, Lacework, CrowdStrike Falcon Intelligence.
Sequence your security investments logically: start with identity and monitoring (highest ROI, lowest deployment friction), then layer in workload and API protection as your infrastructure and compliance requirements mature. The NIST Cybersecurity Framework provides an excellent reference model for structuring controls across each layer and is widely accepted as a compliance benchmark by enterprise buyers evaluating startup vendors.
Step-by-Step Implementation of AI Cloud Security Solutions for Startups
Implementing AI cloud security solutions for startups begins with visibility, followed by monitoring, automation, and continuous optimization.
Step 1: Audit your existing cloud infrastructure. Inventory all cloud accounts, regions, active services, IAM roles, and external-facing resources across Amazon Web Services, Microsoft Azure, and Google Cloud. A free Wiz trial can surface an initial exposure picture within hours — most startups are surprised by what they find.
Step 2: Enable AI monitoring tools across your environment. Deploy your chosen platform with read-only API access. For agentless platforms like Wiz, deployment takes hours. For agent-based solutions like CrowdStrike Falcon, plan a staged rollout starting with production systems and expanding over two to three weeks.
Step 3: Configure automated threat alerts with proper routing. Define your critical asset categories — production databases, customer data stores, authentication systems — and configure high-priority alert routing. Integrate with PagerDuty or Slack so alerts reach the right engineer with full context immediately.
Step 4: Implement least-privilege access across all identities. AI security tools will surface over-permissioned IAM roles and service accounts — often dozens of them. Remediate findings systematically, starting with your highest-risk production identities. This single step consistently delivers the highest security ROI available to lean engineering teams.
Step 5: Continuously monitor cloud activity and track remediation. Establish a weekly review of your security posture dashboard, track remediation rates for open findings in Jira alongside feature work, and run quarterly tabletop exercises to test your incident response playbooks before you need them under real pressure.
Best Practices When Using AI Cloud Security Solutions for Startups
To maximize effectiveness, AI cloud security solutions for startups should be integrated into CI/CD pipelines and daily engineering workflows. Integrate security scanning into your CI/CD pipeline so misconfigurations and vulnerable dependencies are caught before code ships. A misconfiguration caught in code review costs minutes to fix. The same misconfiguration caught after a breach can cost months.
Apply least privilege aggressively and continuously. Every service account, IAM role, and API key should hold only the permissions required for its specific function. Over-permissioned credentials are the most commonly exploited configuration weakness — and the easiest to fix proactively.
Enforce MFA on every human identity with cloud console access — no exceptions. Service accounts should use short-lived credentials and IAM roles, never long-lived API keys stored in environment variables or configuration files checked into version control.
Treat security findings as engineering backlog. Assign ownership of critical findings to specific engineers, track remediation in Jira, and include security metrics in sprint reviews. Security debt compounds exactly like technical debt — with much higher interest rates when it comes due.
For teams building on SaaS architecture specifically, our AI security tools for SaaS startups in 2026 guide covers SaaS-specific threat vectors and the tools best suited to address them at different growth stages.
✅ Startup Cloud Security Baseline Checklist
Use this before considering any environment production-ready:
- Enable CSPM scanning across all cloud accounts (Amazon Web Services, Microsoft Azure, Google Cloud)
- Remove all public cloud exposure — open S3 buckets, permissive security groups, exposed dashboards
- Enforce least-privilege access on every IAM role and service account
- Enable AI anomaly detection and behavioral baselining across all environments
- Configure automated incident response playbooks for your top five threat scenarios
- Integrate security scanning into your CI/CD pipeline (IaC scanning, dependency checks)
- Enable MFA on all human identities with cloud console access — no exceptions
- Establish weekly security posture reviews and remediation tracking
- Rotate all API keys and credentials that have been in use longer than 90 days
- Run a quarterly tabletop incident response exercise with your engineering team
- Document and test your cloud backup and recovery procedures under simulated breach conditions
Limitations of AI Cloud Security Platforms for Startups
AI cloud security solutions for startups are powerful, but they still require tuning, proper configuration, and strong security fundamentals.
False positives remain a persistent challenge. Even the best ML models from CrowdStrike, Wiz, and Lacework generate false positive alerts — particularly during the initial 30–60 day training period before the system has fully characterized your environment’s behavioral baseline. Budget meaningful time for tuning alert thresholds and suppressing known-good behaviors before alert quality peaks.
AI training requirements create a ramp-up period. Behavioral analytics platforms need sufficient historical data to establish meaningful baselines. In new environments — or after significant infrastructure changes — detection accuracy may be reduced until models recalibrate. Plan for additional manual monitoring vigilance during this window.
Configuration complexity is real. Comprehensive platforms like Prisma Cloud by Palo Alto Networks or CrowdStrike Falcon have significant configuration depth. A phased deployment approach — starting with CSPM and anomaly detection, then layering in additional capabilities — consistently outperforms attempts to configure everything simultaneously.
AI security amplifies good fundamentals — it doesn’t replace them. No platform from Wiz, Lacework, CrowdStrike, or Palo Alto Networks eliminates the need for strong IAM hygiene, regular patching, secure coding practices, and incident response planning. AI-driven cloud protection multiplies the effectiveness of a sound security foundation. Without that foundation, you’re automating on top of unresolved risk.
For small businesses navigating similar constraints, our analysis of AI cybersecurity tools for small business in 2026 explores how these limitations play out in resource-constrained environments and what compensating controls work best.
Future of AI Cloud Security Solutions for Startups
The future of AI cloud security solutions for startups is focused on autonomous response, predictive detection, and deeper DevSecOps integration.
Autonomous SOC systems are moving from concept to production. Platforms are beginning to close the loop on incident response — not just detecting threats and alerting humans, but investigating, containing, and remediating incidents end-to-end with minimal human involvement. According to Gartner’s research on AI security operations, autonomous security operations will become a mainstream capability for mid-market organizations by 2027. For startups without dedicated security analysts, this represents a fundamental shift in what lean teams can realistically defend.
Predictive threat detection is maturing beyond reactive anomaly identification. Next-generation platforms are beginning to model full attack paths — analyzing the relationships between vulnerabilities, misconfigurations, and identity exposures across Amazon Web Services, Microsoft Azure, and Google Cloud simultaneously. Wiz‘s security graph and CrowdStrike‘s threat graph are early implementations, showing not just where you’re vulnerable today but how an attacker would chain weaknesses together to reach your most critical assets.
AI-driven DevSecOps security is becoming a baseline buyer expectation. Security scanning in developer IDEs, real-time policy enforcement in CI/CD pipelines, and AI-powered code review for security issues are shifting from advanced features to standard components of modern cloud development. Startups building these practices now will face significantly less friction when enterprise customers begin requiring SOC 2 Type II and ISO 27001 certification as a condition of purchase.
Frequently Asked Questions About AI Cloud Security for Startups
AI cloud security solutions for startups help answer common concerns around cost, implementation, and effectiveness in real-world environments.
What is AI cloud security for startups?
AI cloud security for startups refers to ML-powered platforms that automatically monitor, detect, and respond to threats across cloud environments — including misconfigurations, credential theft, API exploits, and ransomware. These platforms replace manual log review with real-time behavioral analytics and automated response, making enterprise-grade security achievable for lean engineering teams without dedicated security staff.
Is Wiz better than CrowdStrike for startups?
It depends on your stage and priorities. Wiz is better for early-stage startups that need fast, agentless deployment and immediate posture visibility with minimal setup. CrowdStrike Falcon is better for growth-stage startups that need best-in-class runtime threat detection and managed threat hunting. Many mature startups use both — Wiz for CSPM and posture management, CrowdStrike for workload protection and incident response.
How much do AI cloud security tools cost for startups?
Pricing varies significantly. Wiz and Lacework offer flexible, consumption-based pricing with startup programs for early-stage companies. CrowdStrike and Prisma Cloud by Palo Alto Networks typically require larger annual commitments. Budget anywhere from $15,000 to $150,000+ annually depending on your cloud footprint and required capabilities. Startup discounts of 20–40% are common with multi-year commitments — always negotiate.
What is AI cloud security for startups? AI cloud security for startups refers to ML-powered platforms that automatically monitor, detect, and respond to threats across cloud environments — including misconfigurations, credential theft, API exploits, and ransomware. These platforms replace manual log review with real-time behavioral analytics and automated response, making enterprise-grade security achievable for lean engineering teams without dedicated security staff.
Is Wiz better than CrowdStrike for startups? It depends on your stage and priorities. Wiz is better for early-stage startups that need fast, agentless deployment and immediate posture visibility with minimal setup. CrowdStrike Falcon is better for growth-stage startups that need best-in-class runtime threat detection and managed threat hunting. Many mature startups use both — Wiz for CSPM and posture management, CrowdStrike for workload protection and incident response.
How much do AI cloud security tools cost for startups? Pricing varies significantly. Wiz and Lacework offer flexible, consumption-based pricing with startup programs for early-stage companies. CrowdStrike and Prisma Cloud by Palo Alto Networks typically require larger annual commitments. Budget anywhere from $15,000 to $150,000+ annually depending on your cloud footprint and required capabilities. Startup discounts of 20–40% are common with multi-year commitments — always negotiate.
What is the biggest cloud security risk for startups? Cloud misconfiguration is consistently the leading cause of startup cloud breaches, followed by credential theft through exposed API keys and phishing. The Cloud Security Alliance has ranked misconfiguration as the top cloud threat for multiple consecutive years. Both are preventable with proper CSPM tooling and disciplined IAM hygiene.
Can a small DevOps team manage AI cloud security tools? Yes — and this is precisely why AI-driven platforms exist. Tools like Wiz and Lacework are designed to be manageable by small teams, with automated prioritization that surfaces only the alerts that matter. The key is choosing a platform with high automation capability and low configuration overhead relative to your team size. Our best AI security tools for startups 2026 guide covers which platforms are most operationally efficient for lean teams.
Do startups need multi-cloud security coverage? If you’re running workloads on more than one cloud provider — even just using Amazon Web Services for compute and Google Cloud for ML workloads — yes. Multi-cloud security coverage ensures consistent visibility across your entire infrastructure, preventing the blind spots that attackers actively seek out in environments where security coverage is uneven across providers.
Conclusion
Cloud security is no longer something you can defer until you’re bigger. Attackers target startups aggressively precisely because early-stage companies carry valuable data and move fast. Misconfigurations are inevitable in high-velocity development environments. The cost of a breach — measured in data loss, customer trust, regulatory exposure, and runway — can be existential.
Modern AI cloud security tools bring enterprise-grade threat detection, automated incident response, and continuous posture management within reach of lean engineering teams. Whether you’re running on Amazon Web Services with a three-person DevOps team or scaling a multi-cloud SaaS platform across regions, platforms like Wiz, Lacework, CrowdStrike Falcon, and Prisma Cloud by Palo Alto Networks provide the automated intelligence layer your team needs to stay ahead of threats without dedicated security headcount.
The practical takeaway for startup founders: Start with a free CSPM trial to get immediate visibility into your current posture. Remediate your highest-risk misconfigurations first. Enable behavioral analytics and automated alerting. Build security into your CI/CD pipeline. Then scale your security investment proportionally as your company grows.
Security is a competitive advantage in 2026 — not just a cost center. Investors ask about it in due diligence. Enterprise customers require it before signing. Your users trust you with their data whether or not you’ve earned that trust yet.
Start earning it now — before someone else finds what you’ve left open.
📌 Related reading: AI endpoint security for startups | AI threat detection tools | Startup cybersecurity strategies | SaaS security best practices | Best AI security tools for startups | Affordable cybersecurity tools

1 thought on “AI Cloud Security Solutions for Startups: Complete Guide + Best Tools (2026)”