How to Secure a Startup With AI Tools is becoming essential as modern startups face increasingly advanced cyber threats.
If you’re building a startup in 2025, cybersecurity isn’t optional. Hackers actively target early-stage companies because most operate with lean teams and minimal security infrastructure. Building a strong AI-driven startup security posture is now one of the most critical things a founder can do—not just for protecting data, but for protecting the business itself.
This guide covers the threats you face, the AI tools that stop them, and a layered security strategy that scales with your company.
Quick Summary
How to Secure a Startup With AI Tools shows that startups need AI-driven protection because traditional security alone is no longer enough against modern cyberattacks.
- Startups are high-value, low-defense targets—over 43% of cyberattacks hit small businesses
- AI improves threat detection, response speed, and security coverage without requiring a large team
- Core starting stack: AI EDR + email security + cloud posture management (CSPM)
- Biggest risks: phishing, cloud misconfiguration, insider threats, and ransomware
- AI security works best when layered, properly configured, and paired with human oversight
- Start small at seed stage and scale your defense layer by layer as you grow
TL;DR: The Startup AI Security Architecture
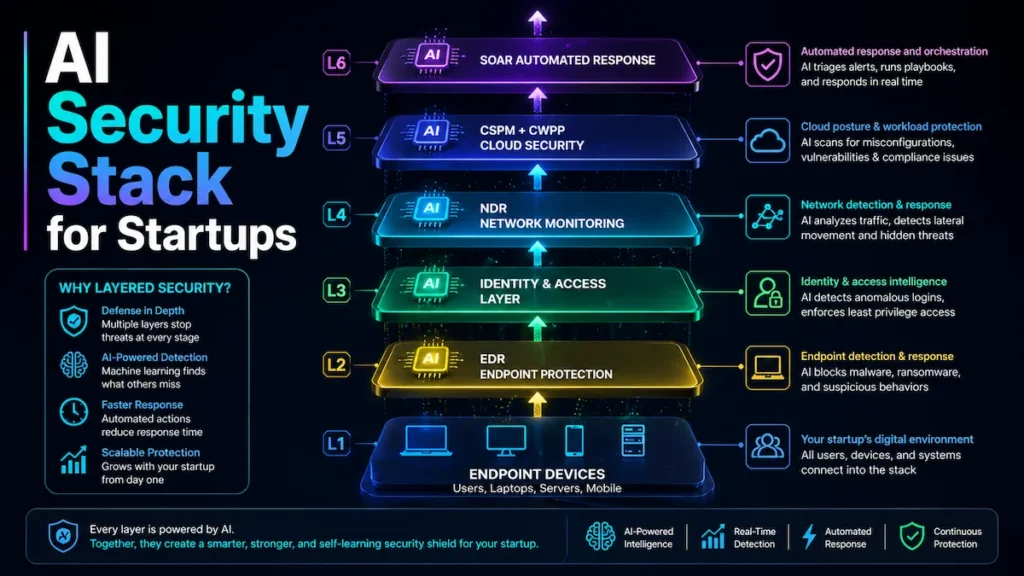
How to Secure a Startup With AI Tools is best understood as a layered defense model that connects endpoints, identity, network, and cloud into one intelligent security system.
Employee Devices → AI EDR → Identity & Access Layer → AI Network Monitoring → Cloud AI Security (CSPM/CWPP) → SOAR Automated ResponseEach layer catches what the previous one misses. Attackers who bypass your endpoint protection get caught at the network layer. Compromised credentials get flagged at the identity layer. Cloud misconfigurations get surfaced before attackers find them. This is the core logic behind modern AI-driven startup security.
Why Startup Security Is Critical in 2025
Understanding How to Secure a Startup With AI Tools helps founders recognize why traditional security methods are no longer enough.
Startups are among the fastest-growing targets for cybercriminals. According to Verizon’s 2024 Data Breach Investigations Report, over 43% of cyberattacks now target small businesses—and most aren’t prepared. Attackers look for companies holding valuable IP, customer data, or payment information with minimal defenses in place.
According to IBM’s Cost of a Data Breach Report 2024, the average breach now costs $4.9 million globally. For an early-stage company, even a fraction of that is catastrophic—often company-ending.
Where AI Security Falls Short (The Honest Truth)
How to Secure a Startup With AI Tools explains how artificial intelligence is reshaping the way startups defend against digital attacks. Before covering what AI does well, founders need to understand where it fails. Skipping this is why many startups end up with false confidence after deploying AI security tools.
False positives create dangerous alert fatigue. Poorly configured AI systems generate enormous alert volumes. When teams are bombarded with hundreds of low-fidelity notifications daily, real threats get buried in the noise. A 2024 Vectra AI survey found that 67% of security analysts said alert fatigue caused them to miss or delay responding to genuine incidents.
Misconfigured tools create blind spots. An AI security tool is only as effective as its deployment. Startups that deploy machine learning monitoring without properly defining their baseline environment end up with models that flag normal activity as suspicious—while missing actual attacker behavior that falls within the misconfigured baseline.
Over-reliance on automation removes critical human judgment. AI automates detection and response, but some threat scenarios require contextual reasoning that no model handles perfectly today. A fully automated response that isolates a critical production server during a false positive can cause more damage than the threat it was trying to stop.
Despite these limitations, AI remains the most scalable security upgrade available to startups today—when implemented correctly with proper configuration and human oversight built in from the start.
Real Breach Case Studies: What Happens Without AI
The most effective way to understand modern startup security is to study what happens when the right tools aren’t in place.
Case Study 1: The Misconfigured Cloud Bucket
How to Secure a Startup With AI Tools becomes ineffective when AI systems are not properly tuned to the startup’s real environment.
A Series A SaaS company running on AWS left an S3 bucket publicly accessible after a routine infrastructure change. The early warning sign that was missed: access logs showed a spike in anonymous GET requests from unfamiliar IP ranges in the 48 hours after the change—a classic automated scanner fingerprint. No one reviewed those logs.
The misconfiguration went undetected for 11 days. An attacker downloaded 2.3 million customer records and listed the data on a dark web forum before the company knew anything had happened.
What failed: No CSPM tool was scanning for misconfigurations. No alerting existed for unusual anonymous access patterns on storage resources.
How AI stops it: A CSPM platform flags public-facing storage buckets the moment they appear and alerts on anomalous access patterns in real time—detection in minutes, not 11 days. This is why AI cloud security solutions are foundational infrastructure, not optional add-ons.
Case Study 2: The Phishing-to-Ransomware Chain
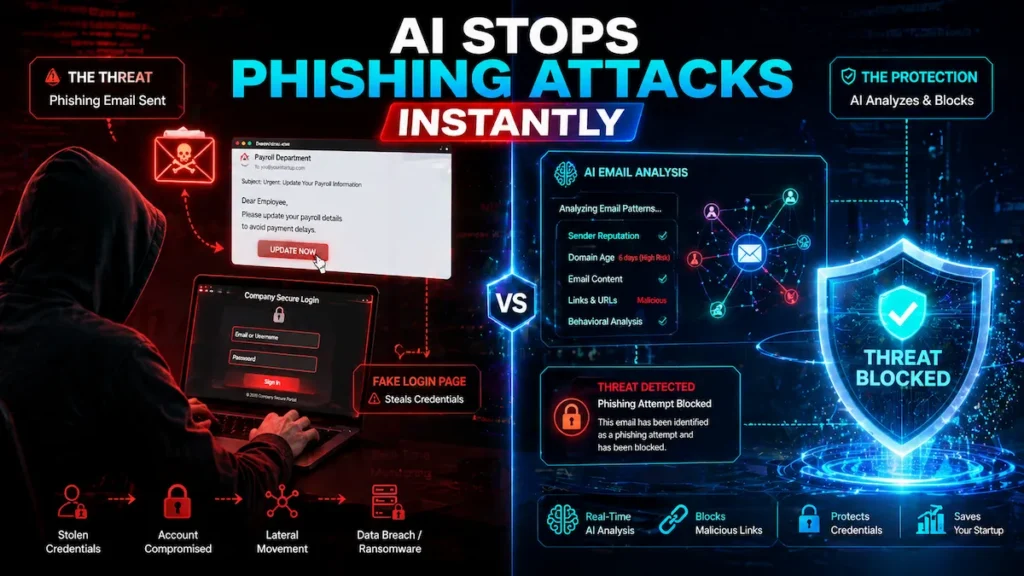
How to Secure a Startup With AI Tools would have blocked the phishing email and stopped ransomware behavior before encryption began.
A 30-person health tech startup received a targeted phishing email impersonating their payroll provider. The early warning sign that was missed: the sending domain had been registered just 6 days prior and had never sent email to anyone in the company before—a signal any behavioral email system would have flagged instantly.
One employee clicked through and entered credentials into a lookalike login page. Within 48 hours, the attacker had mapped internal systems, deleted cloud backups through the compromised admin account, and deployed ransomware across shared drives. The company paid $175,000 in ransom and $90,000 more in incident response and legal costs.
What failed: Legacy email filtering missed the phishing email because the domain had no prior malicious history—the fundamental blind spot of any signature-based system.
How AI stops it: AI email security tools analyze behavioral signals—sender patterns, domain age, link destinations—not just known-bad signatures. The 6-day-old domain would have been flagged before delivery. Simultaneously, AI-powered threat detection would have caught the ransomware’s file encryption behavior within seconds of execution and quarantined the process automatically.
Case Study 3: The Insider Slow Exfiltration
How to Secure a Startup With AI Tools helps detect abnormal user behavior early, even when data theft happens gradually over time.
A pre-IPO fintech company discovered—three months after the fact—that a departing engineer had spent their final two weeks downloading source code, customer data, and financial models to a personal Google Drive account in small daily batches. The early warning sign that was missed: OAuth token logs showed the engineer’s account had granted a personal third-party app access to internal file systems—a high-risk permission that no one reviewed during the offboarding process.
The company only discovered the breach when portions of their codebase appeared in a competitor’s product.
What failed: Their DLP tool was rule-based—it triggered on large single transfers but missed the slow, distributed exfiltration pattern entirely.
How AI stops it: AI-driven UEBA builds a behavioral baseline for every user. The gradual increase in file access volume combined with transfers to personal cloud destinations would have registered as a high-risk anomaly within 24 hours. This is exactly what machine learning intrusion detection is built to surface before the damage compounds.
Common Mistakes Startups Make Before a Breach
Most startup breaches aren’t sophisticated zero-day attacks. They happen because of avoidable gaps deprioritized during early growth. How to Secure a Startup With AI Tools often fails when startups rely only on antivirus, ignore IAM roles, or delay security investments.
Relying only on antivirus—Modern attackers use fileless attacks and polymorphic malware that signature-based tools miss entirely. Antivirus is necessary but nowhere near sufficient.
Ignoring IAM roles—CrowdStrike’s 2024 Global Threat Report documented a sharp increase in cloud identity attacks targeting overpermissioned service accounts in AWS and GCP.
Not enforcing MFA—Microsoft Security research shows MFA blocks over 99% of credential-based attacks. Yet most early-stage startups still don’t enforce it consistently.
Delaying security until Series A—By funding time, most startups have already accumulated significant security debt: misconfigured cloud environments, unpatched systems, and unprotected devices. Fixing it retroactively costs far more than preventing it.
No incident response plan—Without documentation of who does what when an attack hits, response time balloons—and attackers use every extra minute to move laterally.
How AI Is Transforming Startup Cybersecurity
How to Secure a Startup With AI Tools demonstrates how machine learning replaces static rules with adaptive, real-time threat detection.
Traditional security relied on rule-based systems—pre-written definitions of what “bad” looks like. Attackers evolve faster than those rules can keep up.
AI changes this fundamentally. Machine learning models analyze massive volumes of network traffic, user behavior, and system activity in real time, detecting patterns no human analyst or legacy system could catch alone. The NIST Cybersecurity Framework recommends a layered approach across identification, protection, detection, response, and recovery—AI tools now address every layer simultaneously, something that previously required a dedicated SOC team.
For lean startup teams, this means enterprise-grade detection is now accessible without enterprise headcount. Tools built on machine learning intrusion detection can identify attacker behavior at the reconnaissance phase—before any damage is done.
Top Security Threats Startups Face
Phishing Attacks
How to Secure a Startup With AI Tools improves email security by analyzing behavior instead of relying only on known threat signatures.
The most common breach entry point. AI email tools like Abnormal Security and Proofpoint analyze sender behavior, domain age, and link destinations in real time—catching attacks that bypass legacy spam filters because they come from new domains with no prior malicious history.
Ransomware
How to Secure a Startup With AI Tools detects encryption behavior early and stops attacks before full system lockout.
AI threat detection identifies abnormal file encryption behavior the moment it starts—before ransomware finishes executing. SentinelOne uses behavioral AI to quarantine suspicious processes mid-attack, stopping damage rather than recording it.
Insider Threats
UEBA tools establish behavioral baselines per user. Deviations—unusual file access volumes, off-hours activity, transfers to personal cloud storage—are flagged automatically. No full-time analyst required.
Cloud Security Risks
Misconfigured cloud settings remain a leading breach cause. AI cloud security tools continuously scan for exposed buckets, overpermissioned roles, and compliance violations—surfacing problems before attackers find them. See our full breakdown of AI cloud security solutions for startups.
The AI Security Stack: Layered Architecture for Startups
How to Secure a Startup With AI Tools works best when implemented in layers that cover endpoint, identity, network, and cloud security.
Building a secure startup infrastructure works best when you think in layers rather than individual products.
LAYER 5 │ SOAR—Automated response, alert triage, incident playbooks
LAYER 4 │ CSPM + CWPP—Cloud posture management, workload protection
LAYER 3 │ NDR—Network traffic analysis, lateral movement detection
LAYER 2 │ Identity AI—Credential anomaly detection, least-privilege enforcement
LAYER 1 │ EDR—Endpoint protection, behavioral threat detectionEDR vs. XDR vs. NDR: Which Does Your Startup Need?
How to Secure a Startup With AI Tools depends on choosing the right security layer based on company size and infrastructure complexity.
| Technology | Coverage | Best Startup Use Case |
|---|---|---|
| EDR | Devices and endpoints | Catch malware, ransomware, fileless attacks on laptops and servers |
| XDR | Endpoints + network + cloud + email | Unified visibility across the full environment |
| NDR | Network traffic | Detect attackers already inside the network moving laterally |
Practical guidance: Start with EDR at seed stage. Move to XDR as your environment grows more complex. Add NDR at Series B and beyond when network visibility gaps become a meaningful risk. For more on Layer 3, see our AI network security monitoring guide.
Step-by-Step: Building an AI Cybersecurity Stack for Startups
How to Secure a Startup With AI Tools requires a structured rollout starting from endpoint protection and scaling into full automation.
Step 1—Deploy AI-Powered Threat Detection
Start with visibility—you can’t defend what you can’t see. Darktrace uses unsupervised machine learning to model your entire environment and detect deviations in real time. CrowdStrike Falcon combines AI endpoint protection with global threat intelligence feeds. See the best AI security tools for startups to compare options by stage and budget.
Step 2—Implement AI Network Monitoring
Vectra AI identifies attacker behaviors inside the network—compromised accounts scanning internal systems, unusual lateral movement—that don’t trigger traditional perimeter alerts. This is where AI network security monitoring catches threats that have already bypassed endpoint defenses.
Step 3—Automate Security Alerts With SOAR
AI-driven SOAR platforms prioritize alerts by severity, correlate related events, and execute automated response playbooks. An off-hours login from an unusual geography gets automatically blocked and escalated—no human log review required.
Step 4—Deploy AI Email Security
Configure AI-powered filtering at the gateway. Proofpoint, Abnormal Security, and Microsoft Defender for Office 365 analyze every inbound message before it reaches an inbox—flagging suspicious emails in real time and warning employees directly.
Step 5—Pair Data Protection With Zero Trust
AI-driven DLP tools monitor data access and block unauthorized transfers automatically. Combining this with a Zero Trust architecture—where every access request is continuously verified—creates a defense that holds even when credentials are compromised. Our guide on zero trust security tools for startups covers implementation without enterprise complexity.
Startup AI Security Deployment Checklist
How to Secure a Startup With AI Tools is most effective when startups follow a structured checklist across identity, cloud, endpoint, and incident response.
🔐 Identity & Access
- Enforce MFA on all accounts—email, cloud, SaaS, code repositories
- Audit all cloud IAM roles—remove overpermissioned accounts and service roles
- Enable login anomaly detection on your identity provider (Okta, Google Workspace, Microsoft Entra)
- Offboard former employees within 24 hours—revoke all access immediately
- Review OAuth app permissions—remove third-party apps with unnecessary access
☁️ Cloud Security
- Confirm no cloud storage buckets are publicly accessible
- Enable CSPM scanning for misconfigurations across all cloud accounts
- Enable AI-driven vulnerability scanning on all cloud workloads
- Set up automated alerts for anomalous API call volumes and patterns
💻 Endpoint Protection
- Deploy AI-powered EDR on every company device—laptops, servers, remote machines
- Ensure all devices run current OS patches and updates
- Enforce disk encryption on all endpoints
📧 Email Security
- Enable AI email security filtering at the gateway level
- Configure real-time employee warnings for flagged suspicious emails
- Run a phishing simulation to assess current team awareness
🚨 Incident Response
- Document a basic incident response plan—who owns what, which systems to isolate, who to notify
- Implement DLP policy covering cloud storage and email transfers
- Implement SOAR for automated alert triage once your environment grows (Series A+)
- Conduct annual third-party penetration testing

Best AI Security Tools for Startups: Head-to-Head Comparison
How to Secure a Startup With AI Tools involves selecting tools based on startup stage, budget, and required security depth.
| Tool | Best For | Team Size | Core Strength | Pricing |
|---|---|---|---|---|
| CrowdStrike Falcon | Lean teams needing fast EDR deployment | Any size; Falcon Go built for small teams | Industry-leading EDR; global threat intel | Falcon Go ~$5/device/month |
| SentinelOne | Best balance of capability and startup affordability | Seed to growth | Behavioral AI; one-click ransomware rollback | Scalable per-endpoint |
| Darktrace | Mature environments with dedicated security budget | Growth-stage with budget | Self-learning AI; minimal configuration; broadest coverage | Enterprise; contact sales |
| Vectra AI | Teams where network complexity has grown | Series B+ with complex infrastructure | Best-in-class lateral movement detection | Enterprise; contact sales |
For lean teams under 10 people: Start with CrowdStrike Falcon Go or SentinelOne. Both offer AI-powered endpoint protection at accessible price points with minimal setup time.
After funding (Series A+): Darktrace becomes viable when you have budget for broader AI-driven coverage. Add Vectra AI when your network environment grows complex enough that lateral movement detection becomes a meaningful gap.
The Startup Security Maturity Path
| Stage | Security Priority | Estimated Monthly Cost |
|---|---|---|
| Pre-Seed to Seed | EDR + MFA + AI email filtering + cloud bucket audit | $200–$500 for a 10-person team |
| Series A | Add NDR + CSPM + formal IAM policy + incident response plan | $1,000–$3,000 |
| Series B+ | Full SOAR + Zero Trust + XDR + SOC 2 readiness + MSSP | $5,000+ |
Benefits of AI-Driven Startup Security
How to Secure a Startup With AI Tools delivers faster threat detection, reduced workload, and scalable protection for growing teams.
Real-time threat detection—AI operates 24/7 without fatigue, catching threats the moment anomalies appear rather than hours later in a manual log review.
Predictive cybersecurity—Machine learning identifies early warning signals of an attack in progress, giving teams time to respond before damage occurs.
Reduced operational workload—Routine tasks like log analysis, alert triage, and compliance reporting are automated, freeing your team to focus on building product.
Scalability—AI models adapt as your user base and infrastructure grow, without requiring complete reconfiguration at every stage.
Challenges to Plan For
How to Secure a Startup With AI Tools requires careful planning to avoid issues like cost pressure, integration complexity, and alert fatigue.
Cost at early stages—Enterprise-grade platforms like Darktrace are priced for growth-stage companies. Budget for security incrementally from day one rather than trying to fund a full stack at seed.
Alert fatigue from misconfiguration—Poorly deployed AI tools generate excessive false positives that erode team trust in the system. Proper baseline configuration at deployment is not optional.
Integration across fragmented stacks—Prioritize platforms with broad API support and native integrations with the SaaS tools your team already uses.
Skills gap—AI security outputs require people who know how to interpret and act on them. If that expertise doesn’t exist in-house, an MSSP is worth the investment.

The Future of AI in Startup Cybersecurity
How to Secure a Startup With AI Tools is shifting toward autonomous security systems and predictive threat intelligence.
Autonomous SOC systems—AI will increasingly handle alert investigation, event correlation, and incident response without human intervention—bringing SOC-level protection to teams without SOC-level headcount.
Predictive threat intelligence—Models trained on global threat data will anticipate emerging attack patterns before they’re deployed at scale, allowing startups to harden defenses proactively.
Dynamic Zero Trust—Zero Trust will become continuously adaptive, with AI evaluating real-time risk scores and adjusting access permissions based on behavior, location, and device posture. Our guide on zero trust security for startups covers where to start building this architecture today.
Founders who invest in building secure startup infrastructure now are creating a security posture that will remain competitive as both the threat landscape and available AI tools continue to evolve.
Conclusion
How to Secure a Startup With AI Tools ultimately comes down to building layered, proactive defenses before attackers exploit weaknesses.
The three breach case studies in this guide share a common thread: none of those attacks were unstoppable. Every one had an AI-based solution that would have caught it before the damage was done—CSPM for the exposed bucket, behavioral email analysis for the phishing chain, UEBA for the slow insider exfiltration. The technology existed. The companies just hadn’t deployed it.
Building a modern AI cybersecurity stack for startups comes down to one principle: layered, proactive defense deployed before attackers arrive. Start with your highest-risk areas—endpoint, email, and cloud—build toward network monitoring and Zero Trust as you scale, and use the checklist in this guide to track your progress.
The startups that build security into their foundation are the ones that survive and scale. Start before an attacker forces your hand.
FAQ
Can AI prevent cyber attacks for startups?
Yes—but with an important caveat. AI security tools detect and respond to threats in real time, dramatically reducing both the frequency and severity of successful attacks. However, they must be properly configured and paired with human oversight. Poorly deployed AI creates false confidence while leaving real gaps unaddressed.
What are the best AI cybersecurity tools for startups?
For lean teams under 10 people, CrowdStrike Falcon Go and SentinelOne offer the best combination of AI-powered protection and accessible pricing. As you scale, Darktrace provides broader autonomous coverage and Vectra AI adds best-in-class network detection. Start with endpoint and email security, then expand to network monitoring and cloud posture management.
Is AI security affordable for small businesses?
Yes. CrowdStrike Falcon Go starts at approximately $5 per device per month. Microsoft Defender for Business is included in certain Microsoft 365 plans. A basic AI security stack for a 10-person seed-stage startup typically costs $200 to $500 per montha fraction of the cost of a single breach.
How does AI detect cyber threats?
AI analyzes large volumes of data—network traffic, user behavior, file activity, login patterns—and identifies deviations from established baselines. Unlike signature-based tools that only catch known threats, machine learning models detect novel attack behavior, generating alerts or triggering automated responses when anomalies appear.
What is the difference between EDR, XDR, and NDR?
EDR protects individual devices. NDR monitors network traffic and catches attackers who have bypassed endpoint defenses. XDR unifies both into a single platform that also covers cloud and email. For most seed-stage startups, EDR is the right starting point. XDR becomes the better choice as infrastructure complexity grows.
Where does AI security fall short for startups?
Three common failure modes: false positives that create alert fatigue, misconfigured baselines that create blind spots, and over-reliance on automation that removes necessary human judgment. AI is a force multiplier—not a replacement for thoughtful security architecture and active human oversight.
