Startups move fast. And unfortunately, hackers know it.
Most early-stage companies are so focused on growth that security becomes an afterthought — until something goes wrong. A single breach can expose customer data, destroy investor trust, and kill a company overnight. That’s why more founders are building their security stack around zero trust security tools for startups from day one — not after disaster strikes.
Building a solid startup zero trust security strategy doesn’t require a massive budget or a full-time security team. It requires the right tools, applied in the right order. This guide gives you exactly that.
Here’s the reality: most startup breaches are preventable. And most startups don’t fail because of bad ideas — they fail because of preventable mistakes.
✅ Quick Zero Trust Checklist for Startups
Before diving in, here’s what a solid foundation looks like:
- Enable MFA on every account — no exceptions
- Centralize identity management (Okta or JumpCloud)
- Remove all shared or generic login credentials
- Replace your VPN with a ZTNA solution
- Monitor devices and access logs continuously
Keep this checklist open as you read. You’ll know exactly where to start by the end.

What Zero Trust Security Means for Startups
Zero trust security tools for startups redefine how modern businesses think about protecting their data, users, and systems — and understanding the basics is the first step toward building a real defense.
Zero Trust is a security framework built on one essential idea: don’t trust anyone automatically — not even people already inside your own network.
Why Traditional Perimeter Security Fails Startups
Traditional security works like a castle with a moat. Once someone gets past the gate, they’re trusted to move anywhere inside. That model made sense when everyone worked in one office and used company-owned computers.
It’s a dangerous approach for modern startups.
Zero trust tools for startups were built specifically to replace this outdated thinking. Today, teams operate across Slack, Google Workspace, AWS, and dozens of SaaS platforms — all accessed from personal devices and home networks. There’s no single perimeter left to defend. Perimeter-based security creates a false sense of protection that attackers exploit constantly.
The Core Principle of Zero Trust: Never Trust, Always Verify
The best zero trust security tools for startups enforce one rule without exception: verify every user, every device, every time — regardless of where they’re connecting from.
This approach relies on conditional access policies, meaning access is granted based on who you are, which device you’re using, whether your device posture meets security requirements, and whether your behavior looks normal. It dramatically reduces the blast radius of any breach — because even if an attacker gets in, they can’t go far.
According to NIST’s Cybersecurity Framework, identity-centric access control is now a baseline requirement for any organization handling sensitive data — including early-stage startups.
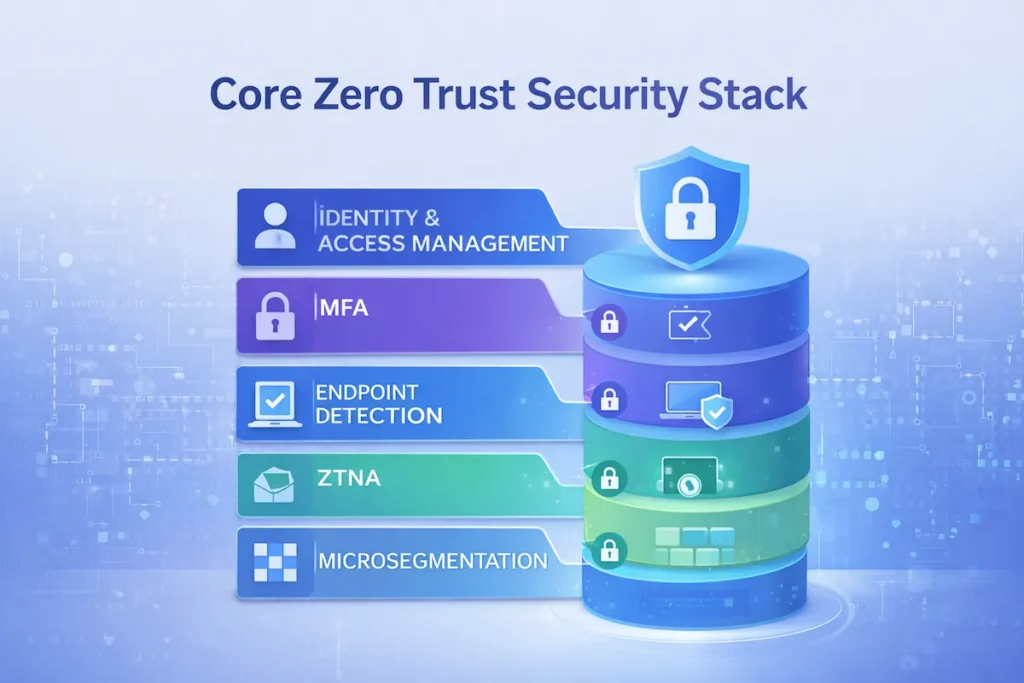
Key Components of a Zero Trust Architecture
Modern startup security tools work together as a layered system — not a single product. The core components include:
- Identity and Access Management (IAM) — controls who can access what, and enforces the least privilege access model
- Multi-Factor Authentication (MFA) — adds a second layer of verification beyond passwords
- Endpoint Detection and Response (EDR) — monitors every device for threats in real time
- Zero Trust Network Access (ZTNA) — replaces traditional VPNs with application-level access control
- Microsegmentation — divides your network into isolated zones to stop lateral movement
You don’t need all of these on day one. But understanding the architecture helps you build toward it systematically.
Why Startups Are Prime Targets for Cyberattacks
Knowing why attackers go after early-stage companies helps explain exactly why zero trust security tools for startups have become a critical investment — not a nice-to-have.
It might seem like hackers only go after large enterprises. The data tells a very different story. Small and mid-sized businesses account for over 40% of all cyberattacks — and startups are especially exposed. Cybercriminals know exactly why.
Limited Security Budgets
Most startups don’t have a dedicated security team. IT responsibilities fall on developers or office managers juggling multiple other priorities. This creates dangerous gaps — particularly around cloud security and AI-powered threat detection — that many founders don’t catch until it’s too late. Zero trust solutions for small businesses help close those gaps without requiring a full-time security hire.
Rapid Cloud Adoption Risks
Startups adopt cloud tools fast — sometimes too fast. SaaS sprawl is real. When employees sign up for tools without IT approval, data ends up scattered across dozens of platforms with inconsistent access controls. Without a centralized identity layer, AI security tools for SaaS startups become essential for maintaining visibility and control across your entire environment.
Remote Workforce Vulnerabilities
Remote work is the norm for most startups. Employees connect from coffee shops, home offices, and co-working spaces — on networks that IT has zero visibility into. Without proper remote workforce security, one compromised device can open the door to your entire cloud environment. Zero trust security tools for startups solve this by enforcing device posture checks before granting any access, regardless of where someone is connecting from.

What Most Zero Trust Guides Don’t Tell You
Most content about zero trust security tools for startups covers the basics — but leaves out the real-world gaps that cause implementations to fail in practice. Most articles walk you through the tools. Few tell you where Zero Trust actually breaks down in practice. Here’s what’s usually left out:
Zero Trust fails without identity hygiene. If your team shares passwords, uses weak credentials, or has dozens of dormant accounts floating around, no tool will save you. Clean up identity first — everything else depends on it.
MFA alone is not Zero Trust. Multi-factor authentication is a critical component — but it’s one layer of a much larger system. Treating MFA as your entire startup zero trust stack is a common and costly mistake.
Tool overload increases risk. More tools don’t mean more security. Startups that bolt on five different security products without a unified strategy often end up with visibility gaps between them. A simpler, well-integrated stack beats a sprawling one every time.
The least privilege access model is non-negotiable. If everyone on your team has admin access because “it’s easier,” you’re one phished account away from a full breach. Scope access tightly — and review it regularly as your team grows.
Essential Categories of Zero Trust Security Tools
Before choosing specific products, it helps to understand the foundational categories that every zero trust security tools for startups stack should be built around.
Before evaluating specific products, understand the categories and what role each plays in your overall zero trust security tools for startups strategy.
Identity and Access Management (IAM)
IAM tools are the foundation of any startup zero trust security framework. They control who can access your systems and enforce the least privilege access model so employees only reach what they genuinely need. Good IAM also enables conditional access policies that adapt based on user behavior, device health, and location — making it the single most impactful investment a startup can make.
Multi-Factor Authentication (MFA)
Zero trust security tools for startups treat MFA as the bare minimum, not the finish line. MFA requires users to verify their identity through a second method — usually an authenticator app or hardware key — beyond just a password. It’s one of the single most effective controls against account takeovers and credential stuffing attacks, and it costs almost nothing to implement.
Endpoint Security and EDR
Endpoint Detection and Response tools monitor laptops, phones, and other devices continuously. They flag unusual behavior, run device posture checks to verify security compliance before granting access, and contain threats before they spread. Modern startup security tools in this category give your team real visibility into what’s happening across every connected device — not just your servers.
Zero Trust Network Access (ZTNA)
ZTNA replaces traditional VPNs with a smarter, more granular approach. Instead of granting access to the full network, ZTNA gives users access only to the specific applications they need. This ties directly to the Secure Access Service Edge (SASE) model, which combines networking and security into a unified cloud-delivered service. Zero trust security tools for startups built on ZTNA scale naturally as your team grows — unlike legacy VPN infrastructure that becomes a liability.
Microsegmentation Tools
Zero trust security tools for startups rely on microsegmentation to prevent attackers from moving laterally across systems. By dividing your network into isolated zones, microsegmentation ensures that a successful breach stays contained. For startups handling sensitive financial, health, or customer data, this layer of protection is no longer optional — it’s an essential part of any mature security posture.
Best Zero Trust Security Tools for Startups
Choosing the right zero trust security tools for startups comes down to fit — your team size, cloud environment, budget, and how fast you need to get protected. Here are five tools that deliver real results for startups — practical, scalable, and worth every dollar.
Okta — Identity-First Zero Trust Platform
Okta is the gold standard for identity-first security. It centralizes access across all your SaaS applications, enforces MFA, and supports granular conditional access policies based on user role, device posture, and location. Okta integrates with thousands of applications and serves as a natural anchor for your broader zero trust security tools for startups stack. Most fast-growing startups eventually standardize on Okta — so starting with it early avoids painful migrations later.
Cloudflare Zero Trust — Secure Network Protection
Cloudflare Zero Trust sits in front of your applications and enforces access policies based on identity, device posture, and location — replacing your VPN entirely. It’s a full ZTNA and SASE platform built for modern cloud environments. Cloudflare offers a strong free plan for up to 50 users, making it one of the most accessible zero trust solutions for small businesses just getting started. As you scale, paid tiers add DNS filtering, data loss prevention, and browser isolation.
JumpCloud — Startup-Friendly Identity Management
JumpCloud is a cloud-based directory platform that handles device management, single sign-on (SSO), and MFA from a single dashboard. It’s designed for lean IT teams and works seamlessly across Mac, Windows, and Linux. If your startup doesn’t want complex enterprise tooling, JumpCloud offers a practical and affordable entry point into zero trust security tools for startups — with a free tier for up to 10 users that’s genuinely useful.
Twingate — Modern Zero Trust Network Access
Twingate is a clean, developer-friendly ZTNA solution that replaces VPNs and gives users access only to the specific resources they need. Setup is fast, the admin interface is intuitive, and it integrates well with cloud-hosted infrastructure. Startups that want fast deployment without heavy configuration should look at Twingate first. It’s particularly well-suited for distributed teams with a mix of cloud and on-premise resources, and it fits naturally into any modern startup zero trust stack.
CrowdStrike Falcon — Advanced Endpoint Security
CrowdStrike Falcon is a leading EDR platform that uses AI-driven threat detection to identify and neutralize attacks across all your endpoints in real time. It performs continuous device posture checks and behavioral analysis that rule-based tools simply can’t match. While positioned more toward growth-stage companies, startups in fintech, healthtech, or legal handling sensitive data should take it seriously. It pairs exceptionally well with a broader AI security strategy for startups and delivers protection that scales as your company does.
How Startups Can Implement Zero Trust Security
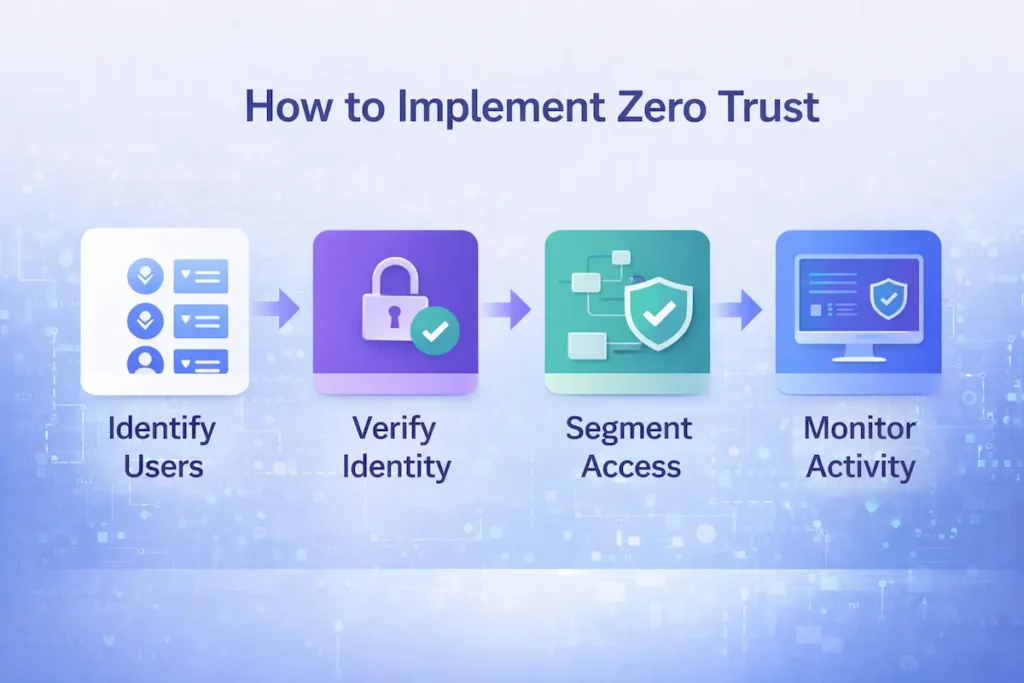
Knowing which zero trust security tools for startups to use is only half the battle — the other half is rolling them out in the right order without disrupting your team. Zero Trust doesn’t have to be an overwhelming overhaul. Here’s a clear, step-by-step path to get there without losing momentum.
Step 1: Identify Users and Devices
Before protecting anything, you need to know what you’re protecting. Audit every user account and every device that accesses your systems. Flag dormant accounts, shared credentials, and personal devices without security controls. Zero trust security tools for startups can only function with a clean, accurate inventory as their foundation — skip this step and everything else is built on sand.
Step 2: Implement Identity Verification
Deploy MFA across all accounts immediately — this is your most impactful first move. Then set up an IAM tool like Okta or JumpCloud to centralize identity management and enforce conditional access policies based on role, location, and device health. This step alone eliminates the majority of common attack vectors. For a broader look at affordable cybersecurity tools for startups at this stage, there are strong options at every budget level.
Step 3: Segment Network Access
Replace your VPN with a ZTNA solution like Twingate or Cloudflare Zero Trust. Define access policies that limit what each user can reach based strictly on their role — enforcing the least privilege access model at the network level. Apply microsegmentation to internal infrastructure to contain any breaches before they spread across your environment.
Step 4: Monitor Activity Continuously
Zero Trust is not a set-and-forget solution. Deploy logging, monitoring, and alerting tools to watch for unusual activity across your environment. Use EDR to monitor endpoints continuously. Review access logs regularly. AI-powered threat detection tools can automate much of this workload — flagging anomalies faster than any human team could catch manually, and responding to incidents before they escalate.
Zero Trust vs Traditional Security
Comparing zero trust security tools for startups against traditional security models makes it clear why the old approach simply doesn’t hold up for modern, cloud-first teams.
| Factor | Traditional Security | Zero Trust Security |
|---|---|---|
| Trust Model | Trust inside network | Never trust, always verify |
| User Access | Broad access once authenticated | Least-privilege, role-based access |
| Remote Work | VPN-based | ZTNA with identity verification |
| Device Posture | Rarely checked | Verified before every access request |
| Breach Containment | Weak — flat network | Strong via microsegmentation |
| Scalability | Limited for cloud | Cloud-native and SaaS-ready |
| Visibility | Limited | Full activity logging and monitoring |
Cost of Zero Trust Security Tools for Startups
One of the biggest misconceptions is that zero trust security tools for startups are only affordable for well-funded companies — in reality, there are strong options at every budget level.
Free Tools Startups Can Start With
Cloudflare Zero Trust offers a generous free tier for up to 50 users. Google Workspace and Microsoft 365 include basic MFA and IAM features at no extra cost. JumpCloud is free for up to 10 users. These starting points already implement core zero trust security tools for startups principles — with zero budget required. There’s no excuse to leave identity completely unprotected.
Affordable SaaS Security Platforms
JumpCloud and Twingate both offer affordable plans for small teams — typically $5–$15 per user per month for core identity and access features. For a detailed side-by-side breakdown, this startup cybersecurity software comparison covers the leading options clearly. If your infrastructure is primarily cloud-based, AI cloud security solutions for startups are also worth reviewing at this stage.
Enterprise-Level Platforms
Okta and CrowdStrike are priced for growth-stage and enterprise companies. Okta’s Workforce Identity plans start around $2–$8 per user per month for core features, scaling up for advanced conditional access and lifecycle management. CrowdStrike pricing varies by module, generally starting at $8–$15 per endpoint per month. For startups handling sensitive customer data, the cost of these tools is far lower than the cost of a breach.
Common Mistakes Startups Make with Zero Trust
Even well-intentioned teams get this wrong — here are the most common pitfalls that undermine zero trust security tools for startups before they ever deliver real protection.
Implementing Tools Without Strategy
Buying security tools without a clear plan is both wasteful and dangerous. Zero trust tools for startups deliver results only when deployed as part of a coherent strategy — with defined policies, ownership, and enforcement. Tools without strategy create a false sense of security that’s often worse than having nothing at all, because it stops founders from taking the threat seriously.
Ignoring Identity Security
Many startups focus entirely on network security while leaving identity completely exposed. Weak passwords, no MFA, and shared accounts are not just oversights — they’re open invitations. Identity is the new perimeter, and protecting it is the single most essential step in any startup zero trust stack. For practical options that make identity hygiene easier to manage at scale, see AI cybersecurity tools for small businesses.
Poor Access Management
Giving every employee admin access because “it’s easier” is one of the most reckless mistakes a startup can make. Enforce the least privilege access model from day one — every user gets access only to what they need for their specific role. Review and update permissions regularly, especially when team members change roles or leave the company. Stale permissions are a dangerous liability that most startups don’t discover until after an incident.
Future of Zero Trust Security for Startups
AI-Driven Cybersecurity Tools
AI is fundamentally changing how threats are detected and neutralized. Zero trust security tools for startups increasingly use machine learning to identify anomalous behavior — flagging threats that rule-based systems miss entirely. As NIST’s Cybersecurity Framework makes clear, continuous monitoring paired with adaptive access controls is becoming the baseline expectation for any serious security posture, regardless of company size.
Automated Threat Detection
Automation is making enterprise-grade security accessible to small teams. Modern zero trust solutions for small businesses with built-in automation can analyze millions of signals in real time and respond to incidents before they escalate. As CISA outlines in its Zero Trust Maturity Model, automated response is the defining characteristic of a mature Zero Trust implementation — and the tools to get there are increasingly within startup reach.
Identity-First Security Models
The future of zero trust security tools for startups is unambiguously identity-first. As networks grow more distributed and perimeters dissolve entirely, user identity becomes the most reliable and enforceable control point. Conditional access policies tied to real-time device posture checks and behavioral signals will become the standard — not the exception. Startups that build this foundation now will be significantly ahead as compliance requirements tighten and investor security scrutiny increases.
Pros and Cons of Zero Trust Security Tools
| Pros | Cons |
|---|---|
| Dramatically reduces breach risk | Takes time to implement correctly |
| Built for remote and distributed teams | Can create user friction if misconfigured |
| Scales naturally with startup growth | Some tools have a learning curve |
| Limits damage from insider threats | Enterprise platforms can be expensive |
| Enforces least privilege by design | Requires ongoing monitoring and review |
| Meets major compliance requirements | Tool sprawl can create new blind spots |
Frequently Asked Questions
What are zero trust security tools?
Zero trust security tools are software solutions that enforce the principle of “never trust, always verify.” They include IAM platforms, MFA solutions, ZTNA products, EDR tools, and microsegmentation software — all designed to verify every user and device before granting access, using conditional access policies and device posture checks as core controls.
Why do startups need zero trust security?
Startups are high-value targets with limited security resources. Zero trust security tools for startups protect cloud environments, remote workers, and sensitive data without requiring a large IT team. More importantly, they prevent the kind of breaches that kill early-stage companies before they have a chance to recover.
Are zero trust tools expensive for small businesses?
Not necessarily. Cloudflare Zero Trust and JumpCloud both offer free tiers for small teams. Paid plans for most startup-friendly tools run $5–$15 per user per month — a fraction of what a single breach costs in lost revenue, legal fees, and customer trust. NIST’s Cybersecurity Framework also provides free guidance for organizations building security programs on limited budgets.
What is the best zero trust tool for startups?
Most startups should begin with Cloudflare Zero Trust for network access and Okta or JumpCloud for identity management. Add CrowdStrike Falcon as you scale or begin handling sensitive data. CISA’s Zero Trust Maturity Model is a useful free reference for deciding which tools to prioritize at each stage of growth.
How do zero trust security tools for startups handle remote employees?
Zero trust security tools for startups verify every remote user’s identity and device posture before granting access to any application — no broad VPN access required. Tools like Cloudflare Zero Trust and Twingate ensure remote employees only reach what their role requires. This makes distributed work significantly safer without adding friction to your team’s daily workflow.
Can zero trust security tools for startups help with compliance requirements?
Yes — zero trust security tools for startups naturally support SOC 2, HIPAA, and GDPR compliance by enforcing least privilege access, logging all activity, and requiring verified identity for every access request. Enterprise customers and regulators increasingly expect these controls before signing contracts. Implementing them early puts you ahead when audits and security reviews arrive.
How long does it take to implement zero trust security tools for startups?
Most startups can deploy the foundational layer of zero trust security tools for startups — MFA, IAM, and ZTNA — within two to four weeks. Tools like JumpCloud and Cloudflare Zero Trust are built for fast setup without a dedicated IT team. A full implementation covering endpoint security and microsegmentation typically takes two to three months.
Conclusion
Security isn’t something you figure out after a breach. By then, the damage is done — and for most startups, it’s irreversible.
Most startups don’t fail because of bad ideas. They fail because of preventable mistakes: no MFA, weak access policies, shared credentials, and zero visibility into what’s happening across their environment. Every one of those is fixable — before an attacker finds it first.
The essential truth is this: the best zero trust security tools for startups have never been more accessible. You don’t need a six-figure budget or a dedicated CISO to build a strong foundation. You need a clear strategy, the right tools, and the discipline to apply them in the right order.
Start with identity. Enforce MFA everywhere. Replace your VPN with ZTNA. Monitor continuously. Apply the least privilege access model from day one. Don’t let a dangerous and entirely preventable incident be the thing that finally makes security a priority.
The checklist is at the top of this article. The tools are in front of you. The only move left is to start.

2 thoughts on “Zero Trust Security Tools for Startups: Complete Guide + Best Solutions”