Most SaaS startups don’t think seriously about security until their first enterprise customer asks for a SOC 2 report. Investing in the right AI security tools for SaaS startups early is no longer optional — it’s the difference between closing your next enterprise deal and losing it to a security review you weren’t prepared for.
By that point, fixing security gaps has already become expensive, slow, and stressful. The engineering team is mid-sprint. The sales deal is on the line. And what started as a “we’ll handle it later” checkbox has quietly become a company-level risk.
Here’s the reality: modern SaaS products run on APIs, cloud infrastructure, and dozens of third-party integrations. That means the attack surface grows every time you add a new feature, onboard a new user, or connect a new tool. Traditional security software — built around known threat signatures and scheduled scans — simply wasn’t designed for that environment.
That’s where AI-powered security tools for SaaS companies come in. They monitor continuously, learn what normal looks like in your environment, and respond to threats automatically — without requiring a full-time security team.
This guide covers the tools worth evaluating, how to choose them, what they actually detect, and the security mistakes to avoid at every stage of growth.
What Are AI Security Tools for SaaS Startup
Most SaaS founders only realize they need AI security tools for SaaS startups after their first enterprise deal falls through over a failed security review.
AI security tools for SaaS startups are platforms that use machine learning and behavioral analytics to monitor, detect, and respond to threats across your cloud infrastructure, SaaS applications, APIs, and user activity — in real time, without requiring a dedicated security team. Unlike traditional rule-based tools that only catch known attack signatures, AI-powered platforms establish behavioral baselines for every user, service, and device in your environment, then automatically flag and contain anything that deviates. For SaaS startups, they replace the need for round-the-clock manual security monitoring at a fraction of the cost of a full in-house security function.
Best AI Security Tools for SaaS Startups: Quick List
Choosing the right AI security tools for SaaS startups comes down to matching platform capabilities against your actual stack, your growth stage, and the specific threats your product is most exposed to.
- CrowdStrike Falcon
- SentinelOne
- Nightfall AI
- Wiz
- Darktrace
- Vectra AI
- AppOmni
- Lacework
- Cyera
Full breakdowns, pricing, and limitations for each tool are covered below.
Why SaaS Startups Need AI-Driven Security Tools
SaaS platforms are structurally attractive targets. Multi-tenant architecture, interconnected APIs, OAuth-connected third-party apps, and cloud infrastructure across multiple providers — each is a potential entry point. Modern attackers aren’t breaking down the front door. They’re slipping in through misconfigured settings and stolen credentials.
Traditional rule-based tools mostly look for known attack signatures — which means they often miss modern SaaS-specific attacks entirely. They run scheduled scans and generate static alerts. In a SaaS environment where hundreds of users, microservices, and integrations are constantly interacting, that approach leaves too many gaps.
What legacy tools typically miss:
- OAuth misconfigurations giving third-party apps access they shouldn’t have
- Account takeovers using valid stolen credentials — no malware, nothing to detect
- Employees signing up for unsanctioned SaaS tools and shadow AI services
- Lateral movement across microservices after an attacker gains initial access
- Insider threats from legitimate users with excessive or stale permissions
According to the 2025 IBM Cost of a Data Breach Report, the average breach cost reached $4.88 million globally — and companies using AI-powered security automation saved an average of $2.22 million per incident. For an early-stage startup, that gap isn’t just financial. It’s existential.

How AI Security Tools Work
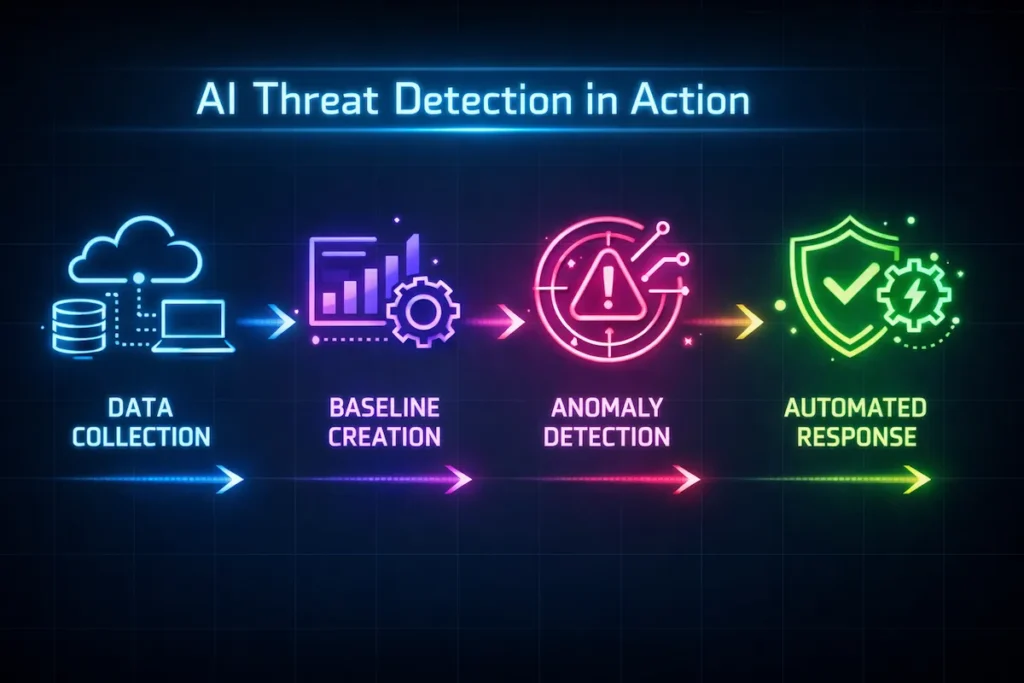
Understanding how AI security tools for SaaS startups actually function helps you evaluate platforms more confidently and avoid paying for capabilities you don’t yet need. Most AI-powered cybersecurity tools for SaaS follow the same four-stage process:
1. Data collection. The platform ingests signals from across your environment — cloud infrastructure logs, identity provider activity (Okta, Auth0), API traffic, SaaS application events, endpoint telemetry, and user behavior data from tools like Slack, GitHub, and Google Workspace.
2. Behavioral baseline creation. Using machine learning, the system builds a behavioral profile for every entity in your environment — each user, service account, API, and device. This baseline reflects what normal looks like: typical login times, typical data access volumes, typical API call patterns.
3. Anomaly detection. When any entity deviates from its baseline — a user accessing data they’ve never touched, an API making calls at unusual volume, a service account accessing a new region — the system flags it automatically. No pre-defined rule required.
4. Automated response. The best platforms don’t just alert. They act: revoking access tokens, suspending accounts, isolating affected services, and delivering full-context alerts to your team — often containing threats in under five minutes.
Modern SaaS security frameworks recommended by OWASP and the Cloud Security Alliance increasingly rely on exactly this behavioral monitoring and zero-trust approach as the baseline for defending cloud-native applications.
AI Security Architecture for SaaS Platforms
A well-secured SaaS platform protects every layer in this chain:
Users
↓
Identity Provider (Okta / Auth0) — behavioral baselines, MFA, anomaly detection
↓
API Gateway — rate limiting, payload inspection, auth failure monitoring
↓
Application Layer (Microservices) — lateral movement detection
↓
Data Layer (Databases / Storage) — classification, DLP, access monitoring
↓
Cloud Infrastructure (AWS / GCP / Azure) — config drift, IAM policy changes
↓
SaaS Integrations (Slack / GitHub / Salesforce) — OAuth auditing, SSPM
↓
AI Security Monitoring Layer — correlates signals across all layers in real timeMany SaaS companies running on Amazon Web Services or Google Cloud rely on AI security monitoring to detect identity anomalies and API misuse across this full stack. A single compromise attempt often touches multiple layers simultaneously — correlating signals across all of them is what makes AI-native detection fundamentally faster than point solutions or manual review.
Key Features of AI Security Tools for SaaS Startups
ot all AI security tools for SaaS startups offer the same depth of coverage — the features that matter most depend on your architecture, your data sensitivity, and your team size.
Most enterprise-grade AI cybersecurity tools provide simultaneous visibility across your entire SaaS stack:
| Layer | What AI Monitors |
|---|---|
| User activity | Login patterns, access times, privilege usage, behavioral baselines |
| API traffic | Request frequency, payload anomalies, auth failures, exfiltration signals |
| Cloud infrastructure | Resource access, configuration drift, IAM policy changes |
| Data flows | Sensitive data movement, DLP violations, encryption gaps |
| Endpoints | Device behavior, unmanaged device access, credential usage |
| SaaS applications | Misconfigurations, OAuth permission scope, third-party connections |
Real-time detection and automated response is the single highest-ROI feature for lean teams. The best SaaS threat detection platforms include automated response playbooks — revoking access tokens, blocking IPs, isolating affected services — and alert your on-call engineer with full context. According to Cybersecurity Insiders’ 2025 AI SOC Report, organizations using this automation reduced incident investigation time by at least 25%.
Machine learning anomaly detection establishes behavioral baselines for every entity in your environment. When something deviates, the system flags it automatically — catching credential-based account takeovers where no malware signature exists.
SaaS Security Posture Management (SSPM) continuously audits your SaaS configuration across every connected app — catching misconfigurations, excessive OAuth permissions, and compliance drift before they become incidents.
Best AI Security Tools for SaaS Startups in 2026
Before diving into each platform, if you want a broader view across all startup types, our in-depth review of the best AI security tools for startups in 2026 covers side-by-side pricing, team-size guidance, and tested recommendations beyond the SaaS-specific stack covered here.
This guide is based on security architectures used by modern SaaS companies running on AWS, Kubernetes, and API-driven infrastructure — covering the platforms that appear most consistently across real startup security stacks at each stage of growth.
Full Feature Comparison Table
The table below breaks down the leading AI security tools for SaaS startups across the five dimensions that matter most for a buying decision.
| Tool | AI Detection | Cloud Security | SaaS Apps | Data Protection | Ideal Stage |
|---|---|---|---|---|---|
| CrowdStrike Falcon | ✔ | ✔ | ✔ | ✔ | Seed+ |
| Nightfall AI | ✔ | ✖ | ✔ | ✔ | Seed+ |
| Lacework | ✔ | ✔ | ✖ | ✔ | Seed+ |
| SentinelOne | ✔ | ✔ | ✖ | ✖ | Seed+ |
| Vectra AI | ✔ | ✔ | ✖ | ✖ | Series A+ |
| Darktrace | ✔ | ✔ | ✔ | ✔ | Series A+ |
| AppOmni | ✔ | ✖ | ✔ | ✔ | Series A+ |
| Wiz | ✔ | ✔ | ✖ | ✔ | Series A+ |
| Cyera | ✔ | ✔ | ✔ | ✔ | Series B+ |
CrowdStrike Falcon
Overview: One of the most widely adopted AI-driven security platforms, combining endpoint protection with SaaS posture management through its Adaptive Shield acquisition.
Key capabilities: Unified threat detection across endpoints, cloud workloads, and SaaS identity signals. Real-time misconfiguration monitoring and AI application risk tracking.
Integrations: AWS, Azure, GCP, Okta, Microsoft 365, Google Workspace, Slack, GitHub.
Pricing: Starts at ~$60/device/year (Falcon Go). Enterprise tiers are quote-based.
Best for: Seed-stage teams that want a single platform covering endpoint and SaaS posture without managing multiple vendors.
Limitations: Full SaaS posture coverage requires additional modules beyond the base Falcon Go plan; costs scale quickly as device count grows.
SentinelOne
Overview: Widely regarded as the best starting point for lean teams. Its autonomous AI engine detects and responds to threats without requiring manual investigation.
Key capabilities: Autonomous endpoint detection and response (EDR), behavioral AI, rollback capabilities for ransomware recovery.
Integrations: AWS, Azure, GCP, Okta, major SIEM platforms.
Pricing: Starts at ~$69/device/year (Singularity Core).
Best for: Founders who aren’t security specialists and need strong endpoint protection with minimal operational overhead.
Limitations: Limited native SaaS application monitoring — pairs best with a dedicated SSPM tool like AppOmni for full SaaS coverage.
Nightfall AI
Overview: Purpose-built for SaaS data protection — scanning Slack, GitHub, Google Drive, Jira, and Confluence for PII, API keys, and credentials using machine learning.
Key capabilities: Real-time DLP across collaboration tools, automated remediation, data encryption policy enforcement.
Integrations: Slack, GitHub, Google Drive, Jira, Confluence, Salesforce, Zendesk.
Pricing: Custom; startup-friendly plans available.
Best for: Seed-stage teams handling sensitive customer data across collaboration tools, especially those on a path toward SOC 2 or HIPAA compliance.
Limitations: Focused specifically on data protection and DLP; not a substitute for endpoint security or cloud infrastructure monitoring.
Wiz
Overview: Agentless cloud security that connects to AWS, GCP, and Azure to surface misconfigurations, vulnerabilities, and identity risks without requiring agents on every workload.
Key capabilities: Cloud security posture management (CSPM), vulnerability prioritization, identity risk, agentless scanning.
Integrations: AWS, Azure, GCP, GitHub, Kubernetes, Terraform.
Pricing: Quote-based; startup programs available.
Best for: Cloud-native SaaS teams that need fast, deep visibility into cloud infrastructure without heavy deployment overhead.
Limitations: Agentless architecture means limited real-time runtime detection compared to agent-based alternatives like Lacework or CrowdStrike.
Darktrace
Overview: Self-learning AI that builds a model of every user and device in your environment, detecting subtle behavioral deviations in real time.
Key capabilities: Autonomous Threat Response, email security, SaaS monitoring, self-learning detection without pre-defined rules.
Integrations: Microsoft 365, Google Workspace, Slack, AWS, Azure, major identity providers.
Pricing: Quote-based; Essentials plans available for smaller teams.
Best for: Series A+ startups in regulated industries that need autonomous threat containment with minimal false positives.
Limitations: Self-learning models require a 4–6 week stabilization period before alert accuracy peaks; initial noise can be high.
Vectra AI
Overview: Specializes in behavioral threat detection across hybrid environments — catching attacks that look like normal traffic.
Key capabilities: Lateral movement detection, privilege escalation alerts, command-and-control identification, hybrid cloud coverage.
Integrations: AWS, Azure, Microsoft 365, major SIEM and SOAR platforms.
Pricing: Enterprise; quote-based.
Best for: Series A+ companies with complex hybrid infrastructure that need to detect sophisticated, low-and-slow attacks.
Limitations: Primarily a detection and investigation platform — automated response capabilities are more limited than Darktrace or CrowdStrike without SOAR integration.
AppOmni
Overview: Continuous SaaS posture monitoring across Microsoft 365, Salesforce, ServiceNow, and Google Workspace.
Key capabilities: SSPM, OAuth connection auditing, misconfiguration detection, compliance reporting.
Integrations: Salesforce, Microsoft 365, Google Workspace, ServiceNow, Slack, GitHub.
Pricing: ~$97,000/year benchmark; enterprise quote-based.
Best for: Series A+ teams with large SaaS application footprints and active SOC 2 or compliance obligations.
Limitations: Pricing makes it inaccessible for most seed-stage companies; limited value without a broad SaaS application estate to monitor.
Lacework
Overview: Cloud-native behavioral anomaly detection across workloads, vulnerabilities, and infrastructure — significantly reducing alert fatigue.
Key capabilities: Behavioral cloud monitoring, vulnerability management, compliance automation, ML-based baseline learning.
Integrations: AWS, Azure, GCP, Kubernetes, Terraform, major CI/CD tools.
Pricing: Consumption-based; startup programs available.
Best for: Engineering-led teams that want deep cloud visibility and can tolerate a configuration ramp-up period.
Limitations: Consumption-based pricing can become unpredictable at scale; requires engineering investment to tune properly during initial deployment.
Cyera
Overview: AI-native data security posture management — discovering, classifying, and protecting sensitive data agentlessly across SaaS, cloud, and on-premise environments.
Key capabilities: Automated data discovery and classification, DLP, compliance mapping, data access governance.
Integrations: AWS, Azure, GCP, Microsoft 365, Salesforce, Snowflake, major databases.
Pricing: Quote-based.
Best for: Series B+ companies handling large volumes of sensitive customer data across complex, distributed environments.
Limitations: Overkill for early-stage startups with a limited data footprint; implementation complexity increases significantly with environment size.
Alternatives to Enterprise AI Security Tools
If your team is also managing physical devices, remote employees, or office infrastructure outside your core SaaS environment, our companion guide on AI security tools for small businesses covers device-level and network security recommendations that complement the SaaS-focused stack covered in this guide.
If enterprise pricing puts the leading AI security tools for SaaS startups out of reach right now, these open-source and lower-cost options address your most critical gaps until you’re ready to scale up. Not every seed-stage startup is ready for enterprise pricing. Here are practical alternatives for early teams:
- Snyk — Developer-first security scanning for code, containers, and open-source dependencies. Free tier available. Ideal for engineering teams that want security embedded in their CI/CD pipeline from day one.
- Trivy — Open-source vulnerability scanner for containers and infrastructure-as-code. No licensing cost, widely used in CI/CD pipelines.
- Falco — Open-source runtime security for Kubernetes workloads. Strong community support and a solid starting point for container-heavy architectures.
- AWS Security Hub / GCP Security Command Center — Native cloud security dashboards included with your cloud account. Good baseline posture visibility at no extra cost before you invest in a dedicated CSPM tool.
- GitHub Advanced Security — Secret scanning, code scanning, and dependency review built into GitHub. Included with GitHub Enterprise and an easy first layer against credential exposure.
- Microsoft Defender for Cloud — Free tier available for Azure workloads; provides basic posture management and threat detection without additional licensing.
- Palo Alto Networks Prisma Cloud — Enterprise-grade CNAPP worth evaluating at Series A+ if you need a single platform covering cloud, containers, and code security.
These won’t replace a dedicated AI security platform as you scale, but they address your most critical early gaps at minimal cost.

How AI Security Tools for SaaS Startups Detect Threats
The core advantage of AI security tools for SaaS startups is that they detect threats based on behavioral deviation rather than known signatures — which means they catch attacks that traditional tools never see.
Behavioral Analytics and Anomaly Detection
Rather than matching known signatures, AI cloud security tools establish what normal looks like for every entity in your environment — users, services, APIs, devices. Deviations trigger investigation. This is exactly how AI-driven security catches credential-based account takeovers where no malware signature exists to detect.
Real-World Example: Stopping a SaaS Account Takeover
This is exactly the kind of scenario AI security tools for SaaS startups are built to handle — a valid credential, a legitimate-looking login, and an attack that leaves no malware trail whatsoever.
- An attacker obtains valid credentials through a phishing campaign. The login looks completely legitimate.
- The AI flags an unusual login location — the user normally accesses from Chicago; this session originates from Eastern Europe at 3 AM local time.
- Within minutes, the attacker begins bulk-exporting customer records via API — far outside the behavioral baseline.
- The system correlates both anomalies — geographic deviation plus abnormal data access — and classifies the session as a high-confidence threat.
- Automated response terminates the session, suspends the account, and delivers a full-context alert to the security team.
Total time from attacker’s first action to containment: under four minutes. Without AI monitoring, this pattern would typically surface during a manual log review — hours or days later, after the damage is done.
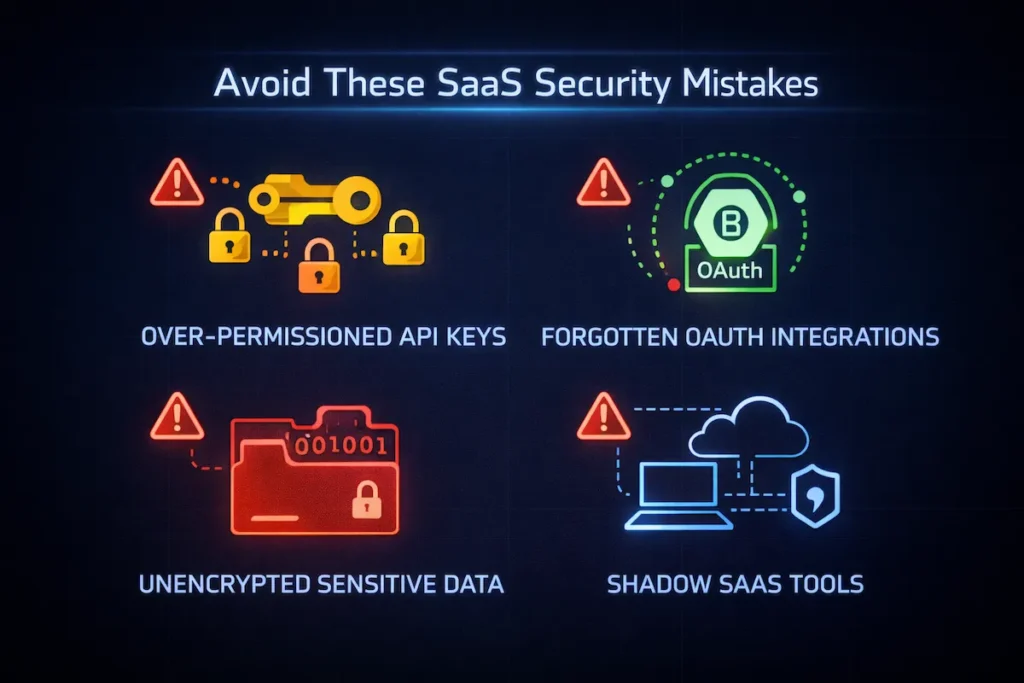
Case Study: SaaS Breach from OAuth Abuse
A Series A SaaS company integrated a third-party analytics tool via OAuth during a product sprint. The integration was granted broad read access to the company’s Google Workspace and Salesforce environments. Twelve months later, the analytics vendor suffered a credential breach. Because the OAuth connection was still active — and the SaaS company had no SSPM tool monitoring third-party permissions — attackers used the vendor’s compromised credentials to access customer records directly through the existing OAuth grant. No password was stolen. No malware was deployed. The breach was discovered three weeks later during a routine audit.
The fix was straightforward: an SSPM tool like AppOmni would have flagged the over-permissioned OAuth connection and alerted the team when the vendor’s access pattern changed. The breach was entirely preventable.
What Happens During Your First AI Security Deployment
One of the most valuable things AI security tools for SaaS startups do in the first 30 days isn’t block attacks — it’s expose the access debt you’ve been accumulating since your first sprint.
Most teams are genuinely surprised by what turns up in the first 30 days. Common discoveries include:
- Dozens of forgotten OAuth connections — integrations from tools no longer in use, still holding active read/write permissions to core systems
- Hundreds of unused service accounts — created during development sprints, never deprovisioned, many with admin-level access
- Over-permissioned GitHub tokens — personal access tokens with repo-wide scope sitting in CI/CD configs
- Unencrypted sensitive data in Slack — API keys, database credentials, and customer PII shared in channels and never deleted
- Shadow SaaS tools — productivity apps signed up by individual team members using Google SSO, completely outside IT visibility
The first deployment isn’t just about protection. It’s a full audit of the access debt you’ve accumulated since day one. Every finding is a breach that hasn’t happened yet.
Example: Real Security Stack by Stage
Seed Stage — Minimum Viable Security:
| Layer | Tool |
|---|---|
| Cloud infrastructure | Wiz or Lacework |
| Data protection | Nightfall AI |
| Identity | Okta or Auth0 (MFA enforced) |
| Endpoint | SentinelOne Singularity Core |
Series A — Adding Depth:
| Layer | Tool |
|---|---|
| Cloud infrastructure | Lacework or Wiz |
| SaaS monitoring | AppOmni |
| Data protection | Nightfall AI |
| Behavioral detection | Vectra AI |
| Endpoint + SaaS posture | CrowdStrike Falcon |
Series B+ — Comprehensive Coverage: Add Cyera for data classification at scale, a dedicated SIEM or AI-powered SOC platform (Microsoft Defender or Palo Alto Networks Cortex XSIAM), and a managed detection and response (MDR) provider for human analyst oversight.
Common Security Mistakes SaaS Startups Make
- Over-permissioned API keys. Service accounts accumulate permissions over time. Audit and scope-limit every key quarterly.
- No monitoring for OAuth integrations. Most startups have no visibility into what permissions third-party connections hold or whether they’re still active.
- Storing secrets in GitHub repositories. Credentials and API keys end up in code — sometimes public repos. Tools like Nightfall catch these automatically.
- Missing API rate limiting. Without rate limiting, a compromised API key can bulk-export your entire customer dataset in a single session.
- Lack of SaaS configuration monitoring. Default configurations in Salesforce, Slack, and Google Workspace are almost never secure enough for production use.
How to Choose the Right AI Security Tools for SaaS Startups
Selecting AI security tools for SaaS startups is less about finding the most feature-rich platform and more about matching the right tool to your actual architecture, team size, and risk profile.
The most common and costly errors that AI security tools for SaaS startups are specifically designed to catch are also the ones most founders never see coming until it’s too late.
- Match tools to your architecture. A single-cloud, API-first product has different needs than a multi-cloud microservices platform handling regulated data.
- Verify integrations with your actual stack. Confirm native integrations with your cloud provider, identity provider, collaboration tools, and logging infrastructure before committing.
- Prioritize identity. Detecting compromised credentials in real time — including OAuth token abuse and over-permissioned service accounts — is the highest-impact capability for most SaaS startups. Most modern breaches begin with identity, not malware.
- Choose the right level of automation. Detection-only tools alert your team. Detection-plus-response platforms contain threats automatically. Fully autonomous platforms act with minimal human involvement — appropriate for Series B+ companies that have validated their security baselines.
- Align cost with your actual risk profile. Start with tools that address your top three risk areas, not the most comprehensive platform on the market.
Pricing Guidance for AI Security Tools for SaaS Startups
The pricing of AI security tools for SaaS startups varies widely by stage — and the published list price is almost never what early-stage companies actually pay once startup programs and negotiations are factored in.
| Tool | Starting Price | Best Stage |
|---|---|---|
| CrowdStrike Falcon Go | ~$60/device/year | Seed to Series A |
| SentinelOne Core | ~$69/device/year | Seed to Series A |
| Nightfall AI | Custom; startup plans available | Seed to Series B |
| Lacework | Consumption-based; startup programs | Seed to Series B |
| Wiz | Quote-based; startup programs | Seed to Series B |
| AppOmni | ~$97,000/year benchmark | Series A+ |
| Vectra AI | Enterprise; quote-based | Series A+ |
| Darktrace | Quote-based; essentials plans | Series A+ |
| Cyera | Quote-based | Series B+ |
Most enterprise vendors have startup programs with meaningfully reduced pricing for pre-Series B companies. Always negotiate from your stage and data volume, not the published list price.
Future of AI Security Tools for SaaS Startups
The next generation of AI security tools for SaaS startups is shifting from reactive threat detection toward predictive, agentic security that identifies attack paths before they are ever exploited.
Agentic AI security is the most significant emerging challenge. As AI agents become embedded in SaaS products — handling customer interactions, processing data, executing workflows — securing their behavior is becoming a new discipline entirely.
AI-driven zero trust architectures are becoming the default for distributed SaaS teams. The zero trust model — no user or service trusted by default — is increasingly enforced dynamically by AI systems evaluating real-time behavioral signals rather than static credentials.
Predictive cybersecurity will shift the model from reactive to proactive. Rather than responding to exploited vulnerabilities, AI systems will increasingly predict likely attack paths based on your specific configuration — enabling remediation before attackers find the gap.
According to CISA’s cybersecurity guidance for organizations, continuous monitoring and rapid incident response are the two capabilities that most consistently reduce breach impact. The next generation of AI security tools delivers both autonomously.
Pros and Cons: AI Security Tools for SaaS Startups
Like any platform category, AI security tools for SaaS startups come with genuine strengths and real tradeoffs — and understanding both helps you set the right expectations before you deploy.
Pros
- Detects unknown and zero-day threats through behavioral analysis, not just known signatures
- Automated response dramatically reduces MTTR for lean teams with no dedicated security staff
- Continuous monitoring covers cloud, APIs, identities, and SaaS apps simultaneously
- Automates SOC 2 and HIPAA compliance evidence collection
- Learns and improves over time as baselines stabilize
Cons
- Requires 2–4 weeks of integration before full coverage is operational
- False positives are common in the first 30–60 days
- Enterprise-tier tools represent significant spend at seed stage
- Autonomous response requires careful configuration — misconfigured playbooks can disrupt legitimate operations
FAQs About AI Security Tools for SaaS Startups
These are the questions founders ask most often when evaluating AI security tools for SaaS startups for the first time.
What are AI security tools for SaaS startups?
AI security tools for SaaS startups are platforms that use machine learning to monitor, detect, and respond to threats across cloud infrastructure, SaaS applications, APIs, and user activity — automatically and in real time, without requiring a full-time security team.
What’s the most important AI security tool for a seed-stage SaaS startup?
The most accessible AI security tools for SaaS startups at seed stage are Wiz or Lacework for cloud misconfiguration detection, combined with Nightfall AI for sensitive data protection across your collaboration stack. Add SentinelOne for endpoint protection and enforce MFA through your identity provider to cover your highest-risk areas first.
How do AI security tools help with SOC 2 compliance?
AI security tools for SaaS startups automate most of what SOC 2 requires — continuous monitoring, audit trails, access anomaly detection, and the compliance documentation auditors need. Platforms like AppOmni and Cyera significantly reduce audit preparation time by maintaining continuous, documented evidence of your security posture automatically.
Are AI security tools effective against insider threats?
Yes — AI security tools for SaaS startups are particularly well-suited to detecting insider threats because behavioral analytics flags legitimate users behaving abnormally, such as accessing unfamiliar data, downloading unusual volumes, or escalating their own permissions. These patterns are caught far more reliably than with signature-based tools that require a known attack pattern to trigger.
How much should a SaaS startup budget for security tools?
A reasonable benchmark when investing in AI security tools for SaaS startups is 10–15% of total infrastructure spend. Most vendors offer startup programs for pre-Series B companies, so start with your highest-risk areas and layer in additional tools as your architecture and budget grow.
Can AI security tools replace a dedicated security team?
They change the ratio dramatically — not eliminate the need entirely. A well-configured AI security stack allows a single security-aware engineer to provide coverage equivalent to a much larger traditional team. But human judgment is still needed for policy-setting, high-severity alert review, and governance decisions.
Conclusion
Most SaaS startups underinvest in security until an enterprise prospect asks hard questions — or until something goes wrong. Neither is a good forcing function.
AI-powered security tools for SaaS companies change the calculus. They monitor continuously, learn what normal looks like in your specific environment, and respond to threats automatically — often before your team knows something happened. Whether you’re a seed-stage team deploying Wiz and Nightfall for the first time, or a Series B company building out a full stack with CrowdStrike, Vectra AI, AppOmni, and Cyera, there are mature, proven options at every stage of growth.
The SaaS startups that treat security as a competitive differentiator — not a compliance checkbox — will be the ones that earn enterprise trust and close deals at scale.
Quick Security Checklist for SaaS Startups
- Audit all active OAuth integrations and revoke unused connections
- Enforce MFA for every user account and service account
- Monitor API traffic for anomalies and implement rate limiting
- Deploy cloud misconfiguration scanning (CSPM)
- Scan collaboration tools for exposed credentials and PII
- Review and scope-limit all API keys and service account permissions quarterly
- Begin SOC 2 Type II preparation — document your data flows and access controls
- Establish a behavioral baseline before your next funding round
